CVE-2024-26152 (GCVE-0-2024-26152)
Vulnerability from cvelistv5 – Published: 2024-02-22 21:52 – Updated: 2024-08-14 15:32
VLAI
Title
Label Studio vulnerable to Cross-site Scripting if `<Choices>` or `<Labels>` are used in labeling config
Summary
### Summary
On all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.
### Details
Need permission to use the "data import" function. This was reproduced on Label Studio 1.10.1.
### PoC
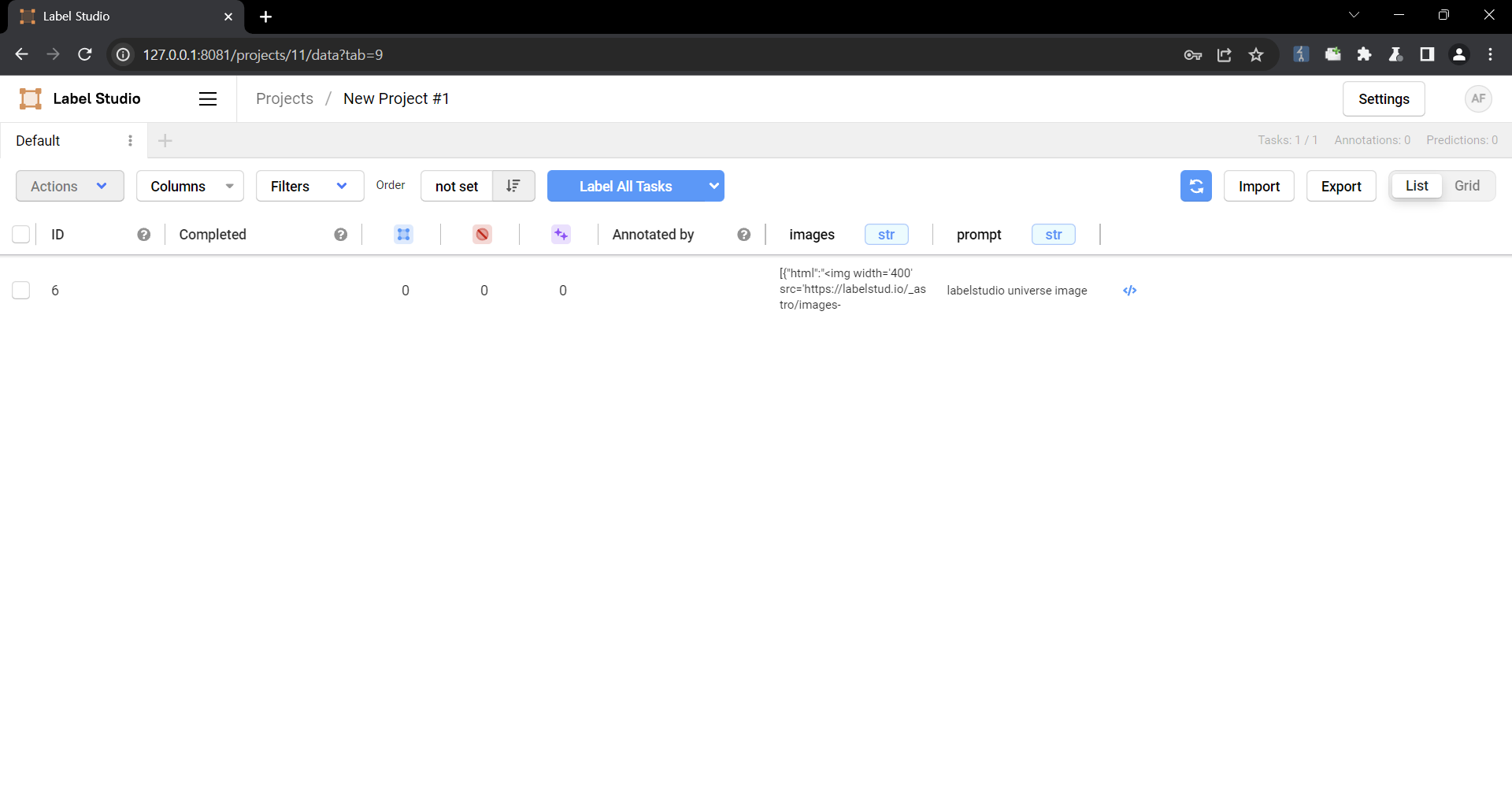
1. Create a project.

2. Upload a file containing the payload using the "Upload Files" function.


The following are the contents of the files used in the PoC
```
{
"data": {
"prompt": "labelstudio universe image",
"images": [
{
"value": "id123#0",
"style": "margin: 5px",
"html": "<img width='400' src='https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif' onload=alert(document.cookie)>"
}
]
}
}
```
3. Select the text-to-image generation labeling template of Ranking and scoring


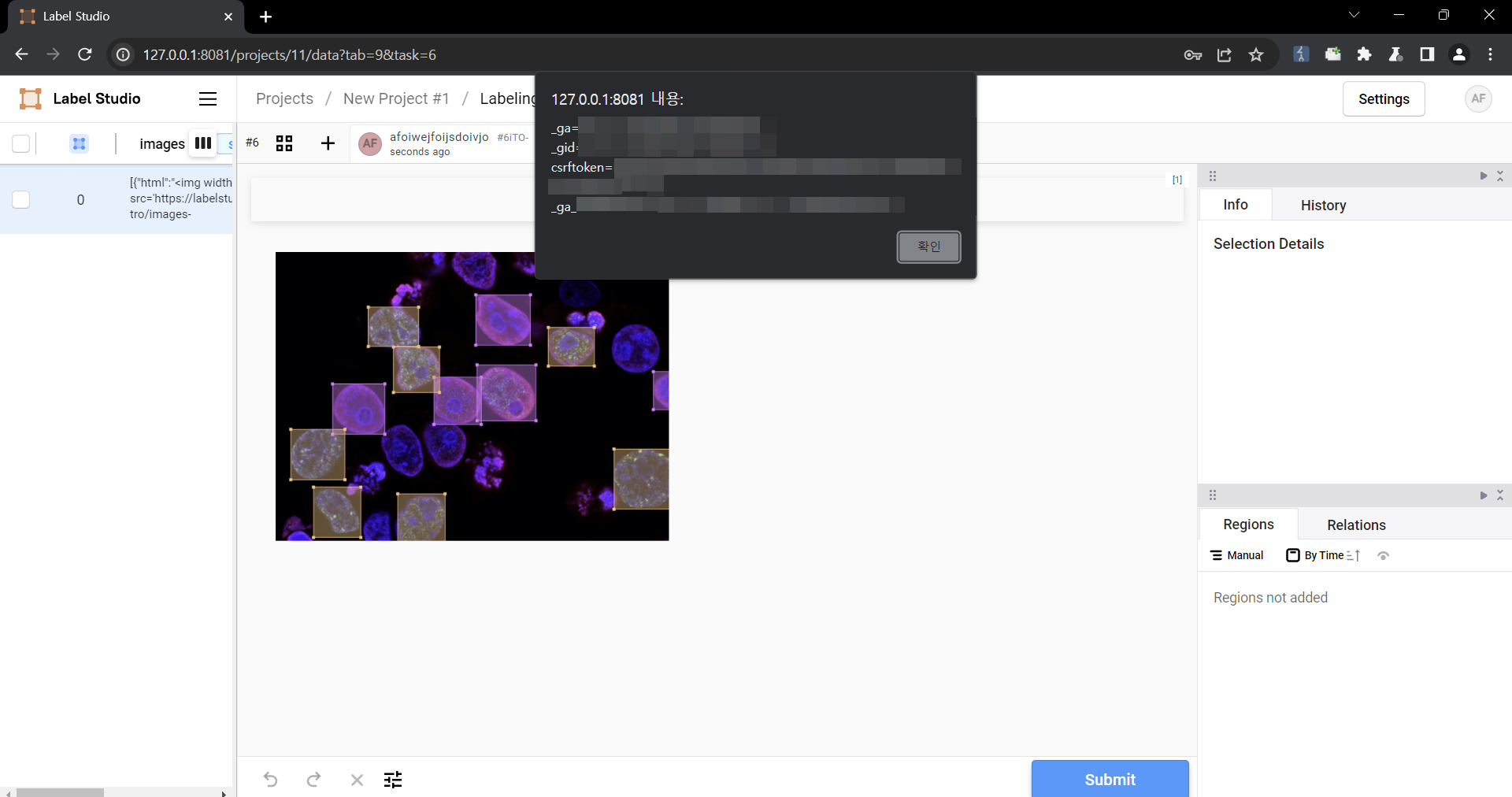
4. Select a task
5. Check that the script is running
### Impact
Malicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.
Severity
4.7 (Medium)
SSVC
Exploitation: poc
Automatable: no
Technical Impact: partial
CISA Coordinator (v2.0.3)
CWE
- CWE-79 - Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')
Assigner
References
4 references
| URL | Tags |
|---|---|
| https://github.com/HumanSignal/label-studio/secur… | x_refsource_CONFIRM |
| https://github.com/HumanSignal/label-studio/pull/5232 | x_refsource_MISC |
| https://github.com/HumanSignal/label-studio/commi… | x_refsource_MISC |
| https://github.com/HumanSignal/label-studio/relea… | x_refsource_MISC |
Impacted products
2 products
| Vendor | Product | Version | |
|---|---|---|---|
| HumanSignal | label-studio |
Affected:
< 1.11.0
|
|
| humansignal | label_studio |
Affected:
0 , < 1.11.0
(custom)
cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:* |
{
"containers": {
"adp": [
{
"providerMetadata": {
"dateUpdated": "2024-08-01T23:59:32.696Z",
"orgId": "af854a3a-2127-422b-91ae-364da2661108",
"shortName": "CVE"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg",
"tags": [
"x_refsource_CONFIRM",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg"
},
{
"name": "https://github.com/HumanSignal/label-studio/pull/5232",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/pull/5232"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8"
},
{
"name": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
}
],
"title": "CVE Program Container"
},
{
"affected": [
{
"cpes": [
"cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:*"
],
"defaultStatus": "unknown",
"product": "label_studio",
"vendor": "humansignal",
"versions": [
{
"lessThan": "1.11.0",
"status": "affected",
"version": "0",
"versionType": "custom"
}
]
}
],
"metrics": [
{
"other": {
"content": {
"id": "CVE-2024-26152",
"options": [
{
"Exploitation": "poc"
},
{
"Automatable": "no"
},
{
"Technical Impact": "partial"
}
],
"role": "CISA Coordinator",
"timestamp": "2024-02-23T14:32:49.819252Z",
"version": "2.0.3"
},
"type": "ssvc"
}
}
],
"providerMetadata": {
"dateUpdated": "2024-08-14T15:32:05.054Z",
"orgId": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"shortName": "CISA-ADP"
},
"title": "CISA ADP Vulnrichment"
}
],
"cna": {
"affected": [
{
"product": "label-studio",
"vendor": "HumanSignal",
"versions": [
{
"status": "affected",
"version": "\u003c 1.11.0"
}
]
}
],
"descriptions": [
{
"lang": "en",
"value": "### Summary\nOn all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.\n\n### Details\nNeed permission to use the \"data import\" function. This was reproduced on Label Studio 1.10.1.\n\n### PoC\n\n1. Create a project.\n\n\n2. Upload a file containing the payload using the \"Upload Files\" function.\n\n\n\nThe following are the contents of the files used in the PoC\n```\n{\n \"data\": {\n \"prompt\": \"labelstudio universe image\",\n \"images\": [\n {\n \"value\": \"id123#0\",\n \"style\": \"margin: 5px\",\n \"html\": \"\u003cimg width=\u0027400\u0027 src=\u0027https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif\u0027 onload=alert(document.cookie)\u003e\"\n }\n ]\n }\n}\n```\n\n3. Select the text-to-image generation labeling template of Ranking and scoring\n\n\n\n4. Select a task\n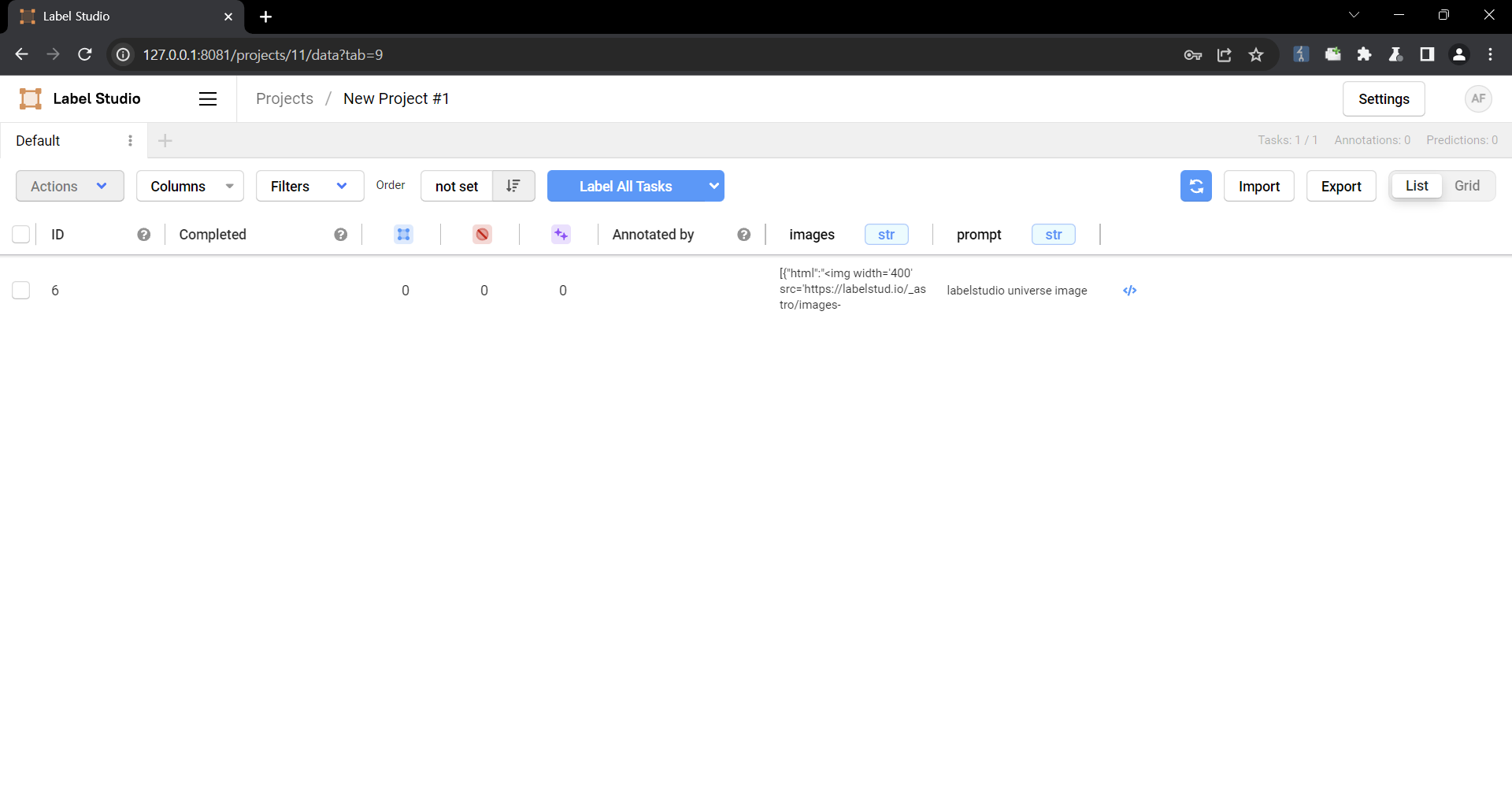\n\n5. Check that the script is running\n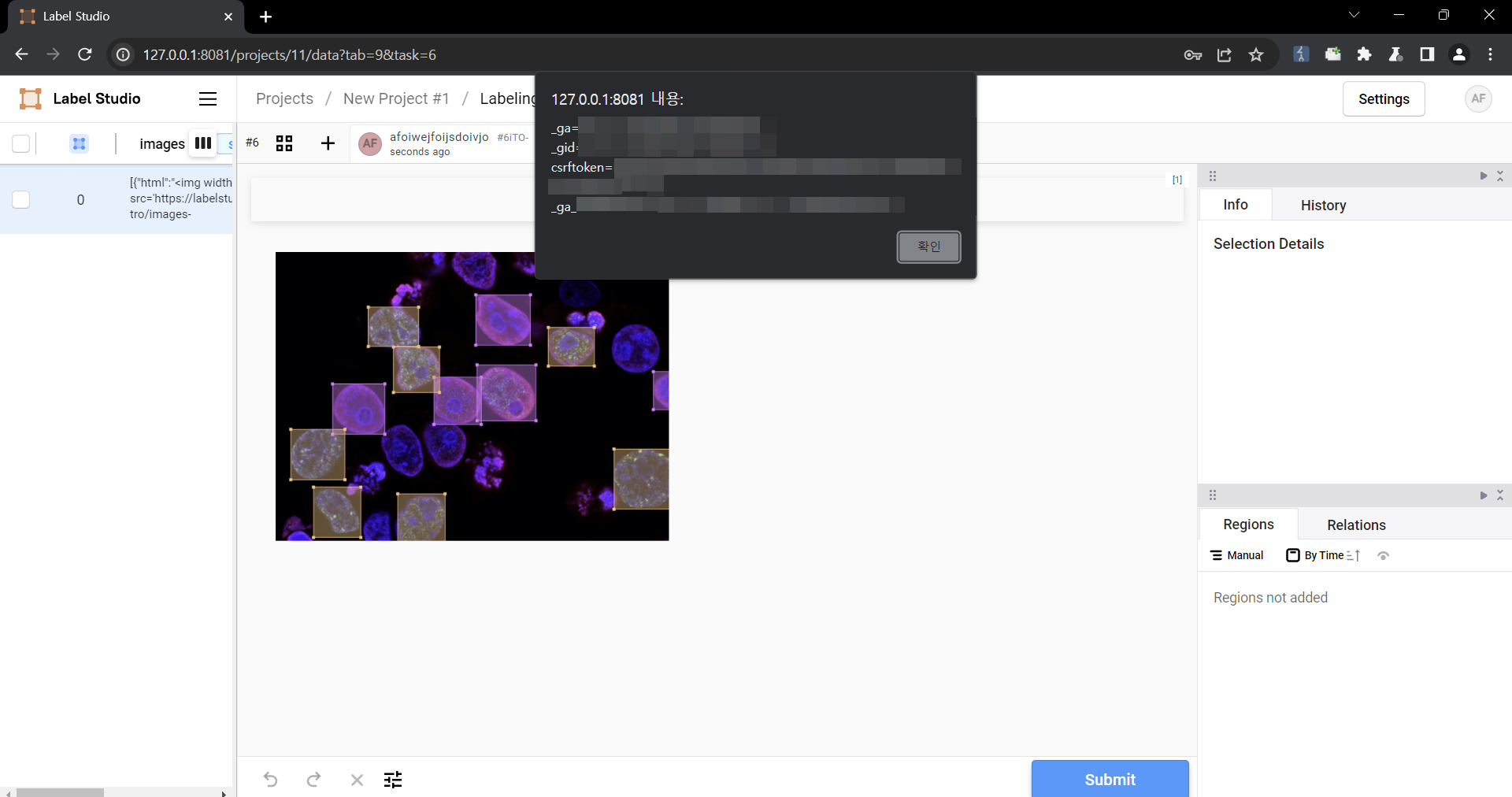\n\n### Impact\nMalicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.\n"
}
],
"metrics": [
{
"cvssV3_1": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N",
"version": "3.1"
}
}
],
"problemTypes": [
{
"descriptions": [
{
"cweId": "CWE-79",
"description": "CWE-79: Improper Neutralization of Input During Web Page Generation (\u0027Cross-site Scripting\u0027)",
"lang": "en",
"type": "CWE"
}
]
}
],
"providerMetadata": {
"dateUpdated": "2024-02-22T21:52:26.193Z",
"orgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"shortName": "GitHub_M"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg",
"tags": [
"x_refsource_CONFIRM"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg"
},
{
"name": "https://github.com/HumanSignal/label-studio/pull/5232",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/pull/5232"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8"
},
{
"name": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
}
],
"source": {
"advisory": "GHSA-6xv9-957j-qfhg",
"discovery": "UNKNOWN"
},
"title": "Label Studio vulnerable to Cross-site Scripting if `\u003cChoices\u003e` or `\u003cLabels\u003e` are used in labeling config "
}
},
"cveMetadata": {
"assignerOrgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"assignerShortName": "GitHub_M",
"cveId": "CVE-2024-26152",
"datePublished": "2024-02-22T21:52:26.193Z",
"dateReserved": "2024-02-14T17:40:03.690Z",
"dateUpdated": "2024-08-14T15:32:05.054Z",
"state": "PUBLISHED"
},
"dataType": "CVE_RECORD",
"dataVersion": "5.1",
"vulnerability-lookup:meta": {
"epss": {
"cve": "CVE-2024-26152",
"date": "2026-06-02",
"epss": "0.0174",
"percentile": "0.82842"
},
"fkie_nvd": {
"descriptions": "[{\"lang\": \"en\", \"value\": \"### Summary\\nOn all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.\\n\\n### Details\\nNeed permission to use the \\\"data import\\\" function. This was reproduced on Label Studio 1.10.1.\\n\\n### PoC\\n\\n1. Create a project.\\n\\n\\n2. Upload a file containing the payload using the \\\"Upload Files\\\" function.\\n\\n\\n\\nThe following are the contents of the files used in the PoC\\n```\\n{\\n \\\"data\\\": {\\n \\\"prompt\\\": \\\"labelstudio universe image\\\",\\n \\\"images\\\": [\\n {\\n \\\"value\\\": \\\"id123#0\\\",\\n \\\"style\\\": \\\"margin: 5px\\\",\\n \\\"html\\\": \\\"\u003cimg width=\u0027400\u0027 src=\u0027https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif\u0027 onload=alert(document.cookie)\u003e\\\"\\n }\\n ]\\n }\\n}\\n```\\n\\n3. Select the text-to-image generation labeling template of Ranking and scoring\\n\\n\\n\\n4. Select a task\\n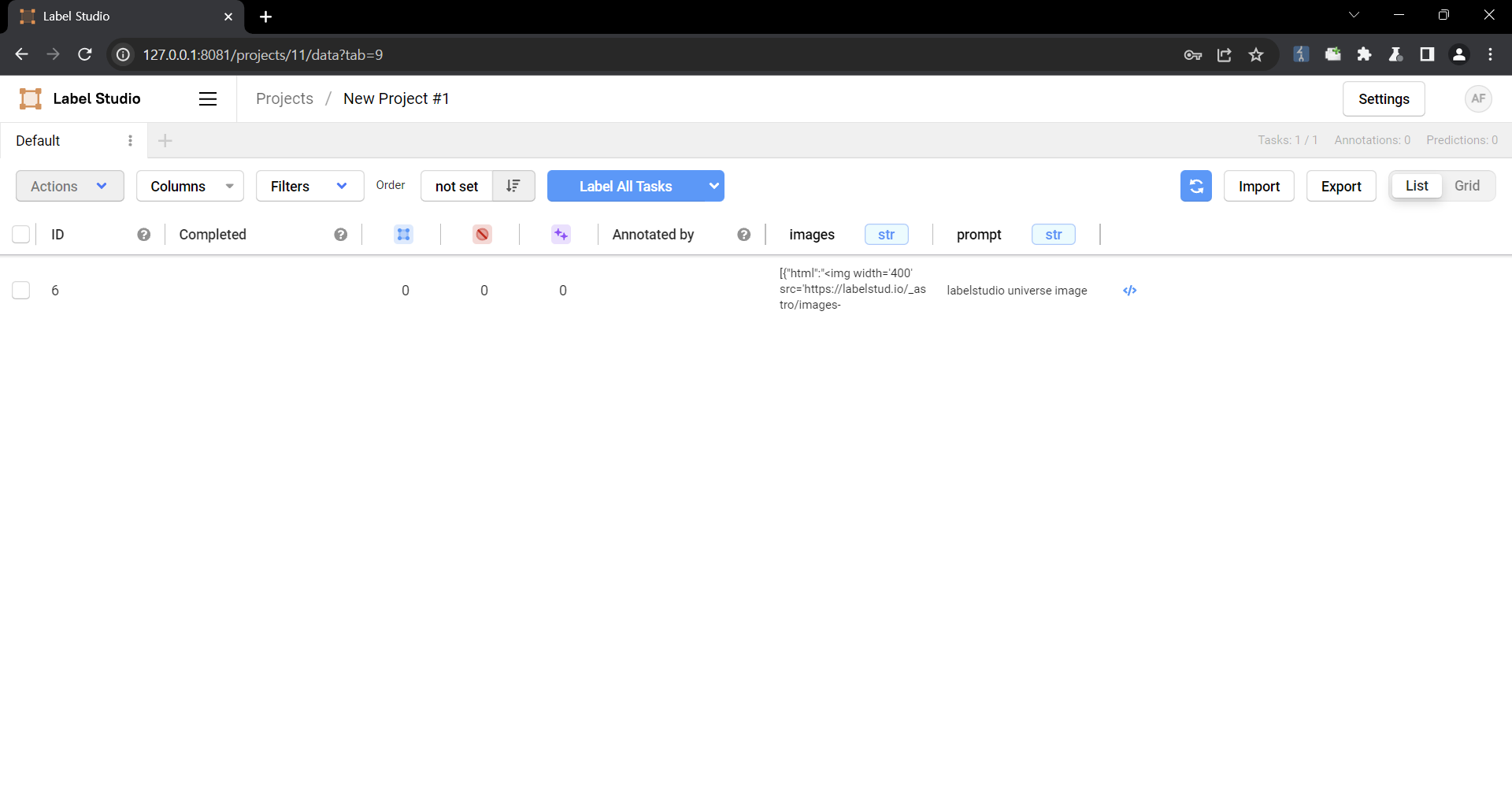\\n\\n5. Check that the script is running\\n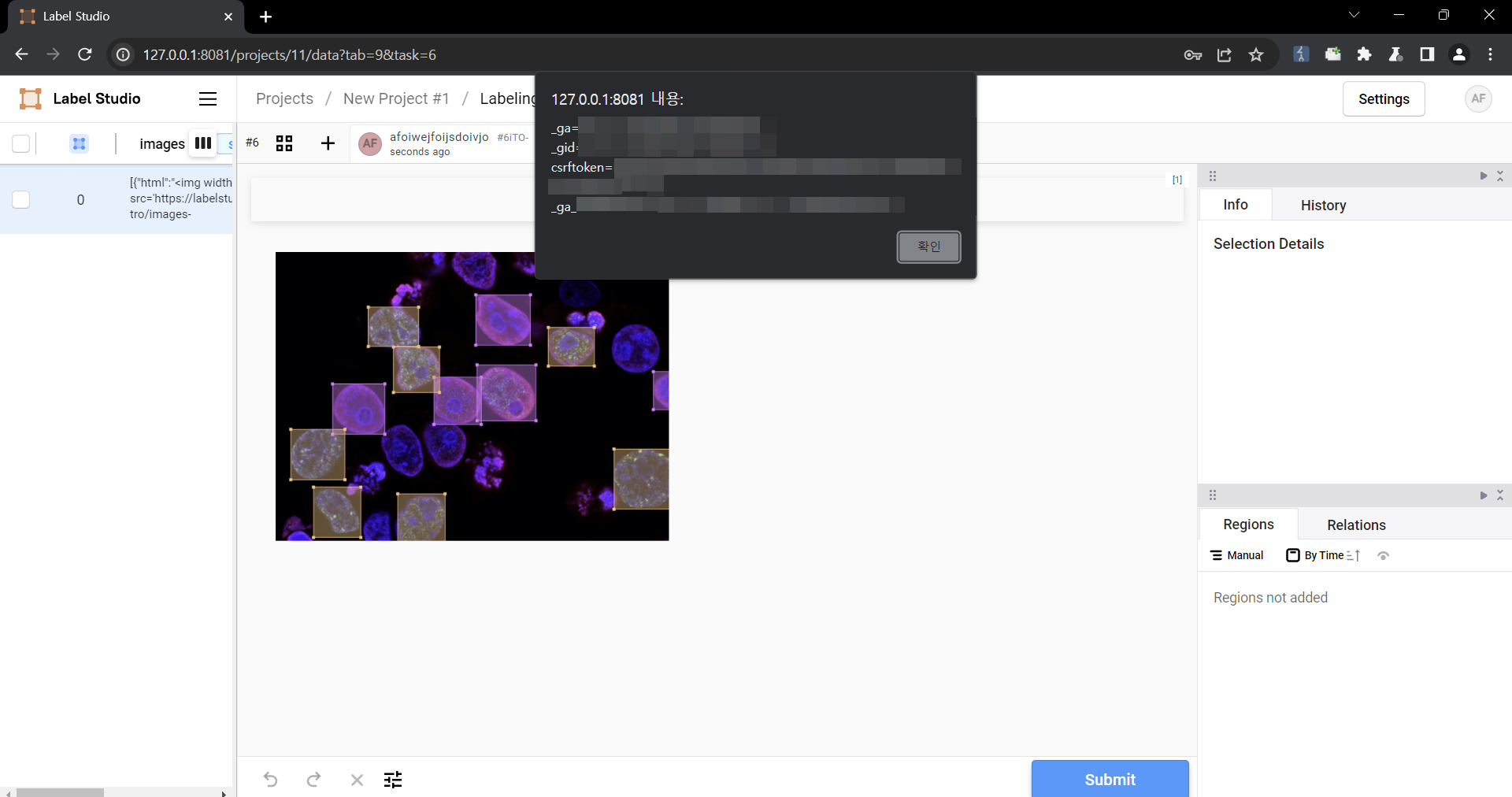\\n\\n### Impact\\nMalicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.\\n\"}, {\"lang\": \"es\", \"value\": \"### Resumen En todas las versiones de Label Studio anteriores a la 1.11.0, los datos importados mediante la funci\\u00f3n de carga de archivos no se desinfectan adecuadamente antes de procesarse dentro de [`Choices`](https://labelstud.io/tags/choices) o [`Labels`](https://labelstud.io/tags/labels), lo que genera una vulnerabilidad XSS. ### Detalles Necesita permiso para utilizar la funci\\u00f3n \\\"importaci\\u00f3n de datos\\\". Esto fue reproducido en Label Studio 1.10.1. ### PoC 1. Cree un proyecto.  2. Cargue un archivo que contenga la carga \\u00fatil usando la funci\\u00f3n \\\"Cargar archivos\\\" .   Los siguientes son los contenidos de los archivos utilizados en el PoC ``` { \\\"data\\\": { \\\" Prompt\\\": \\\"imagen del universo de labelstudio\\\", \\\"images\\\": [ { \\\"value\\\": \\\"id123#0\\\", \\\"style\\\": \\\"margin: 5px\\\", \\\"html\\\": \\\"\\\" } ] } } ``` 3. Seleccione la plantilla de etiquetado de generaci\\u00f3n de texto a imagen de Clasificaci\\u00f3n y puntuaci\\u00f3n 4. \\u00a1Seleccione una tarea! [4 Seleccione una tarea](https://github.com/HumanSignal/label-studio/assets/3943358/71856b7a-2b1f-44ea-99ab-fc48bc20caa7) 5. \\u00a1Compruebe que el script se est\\u00e9 ejecutando! [5 Compruebe que el script se est\\u00e9 ejecutando](https://github.com/ HumanSignal/label-studio/assets/3943358/e396ae7b-a591-4db7-afe9-5bab30b48cb9) ### Impacto Se pueden inyectar scripts maliciosos en el c\\u00f3digo y, cuando se vinculan con vulnerabilidades como CSRF, pueden causar un da\\u00f1o a\\u00fan mayor. En particular, puede convertirse en una fuente de nuevos ataques, especialmente cuando se vincula a la ingenier\\u00eda social.\"}]",
"id": "CVE-2024-26152",
"lastModified": "2024-11-21T09:02:02.457",
"metrics": "{\"cvssMetricV31\": [{\"source\": \"security-advisories@github.com\", \"type\": \"Secondary\", \"cvssData\": {\"version\": \"3.1\", \"vectorString\": \"CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N\", \"baseScore\": 4.7, \"baseSeverity\": \"MEDIUM\", \"attackVector\": \"NETWORK\", \"attackComplexity\": \"LOW\", \"privilegesRequired\": \"NONE\", \"userInteraction\": \"REQUIRED\", \"scope\": \"CHANGED\", \"confidentialityImpact\": \"LOW\", \"integrityImpact\": \"NONE\", \"availabilityImpact\": \"NONE\"}, \"exploitabilityScore\": 2.8, \"impactScore\": 1.4}]}",
"published": "2024-02-22T22:15:47.310",
"references": "[{\"url\": \"https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8\", \"source\": \"security-advisories@github.com\"}, {\"url\": \"https://github.com/HumanSignal/label-studio/pull/5232\", \"source\": \"security-advisories@github.com\"}, {\"url\": \"https://github.com/HumanSignal/label-studio/releases/tag/1.11.0\", \"source\": \"security-advisories@github.com\"}, {\"url\": \"https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg\", \"source\": \"security-advisories@github.com\"}, {\"url\": \"https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8\", \"source\": \"af854a3a-2127-422b-91ae-364da2661108\"}, {\"url\": \"https://github.com/HumanSignal/label-studio/pull/5232\", \"source\": \"af854a3a-2127-422b-91ae-364da2661108\"}, {\"url\": \"https://github.com/HumanSignal/label-studio/releases/tag/1.11.0\", \"source\": \"af854a3a-2127-422b-91ae-364da2661108\"}, {\"url\": \"https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg\", \"source\": \"af854a3a-2127-422b-91ae-364da2661108\"}]",
"sourceIdentifier": "security-advisories@github.com",
"vulnStatus": "Awaiting Analysis",
"weaknesses": "[{\"source\": \"security-advisories@github.com\", \"type\": \"Secondary\", \"description\": [{\"lang\": \"en\", \"value\": \"CWE-79\"}]}]"
},
"nvd": "{\"cve\":{\"id\":\"CVE-2024-26152\",\"sourceIdentifier\":\"security-advisories@github.com\",\"published\":\"2024-02-22T22:15:47.310\",\"lastModified\":\"2025-05-16T14:18:25.530\",\"vulnStatus\":\"Analyzed\",\"cveTags\":[],\"descriptions\":[{\"lang\":\"en\",\"value\":\"### Summary\\nOn all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.\\n\\n### Details\\nNeed permission to use the \\\"data import\\\" function. This was reproduced on Label Studio 1.10.1.\\n\\n### PoC\\n\\n1. Create a project.\\n\\n\\n2. Upload a file containing the payload using the \\\"Upload Files\\\" function.\\n\\n\\n\\nThe following are the contents of the files used in the PoC\\n```\\n{\\n \\\"data\\\": {\\n \\\"prompt\\\": \\\"labelstudio universe image\\\",\\n \\\"images\\\": [\\n {\\n \\\"value\\\": \\\"id123#0\\\",\\n \\\"style\\\": \\\"margin: 5px\\\",\\n \\\"html\\\": \\\"\u003cimg width=\u0027400\u0027 src=\u0027https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif\u0027 onload=alert(document.cookie)\u003e\\\"\\n }\\n ]\\n }\\n}\\n```\\n\\n3. Select the text-to-image generation labeling template of Ranking and scoring\\n\\n\\n\\n4. Select a task\\n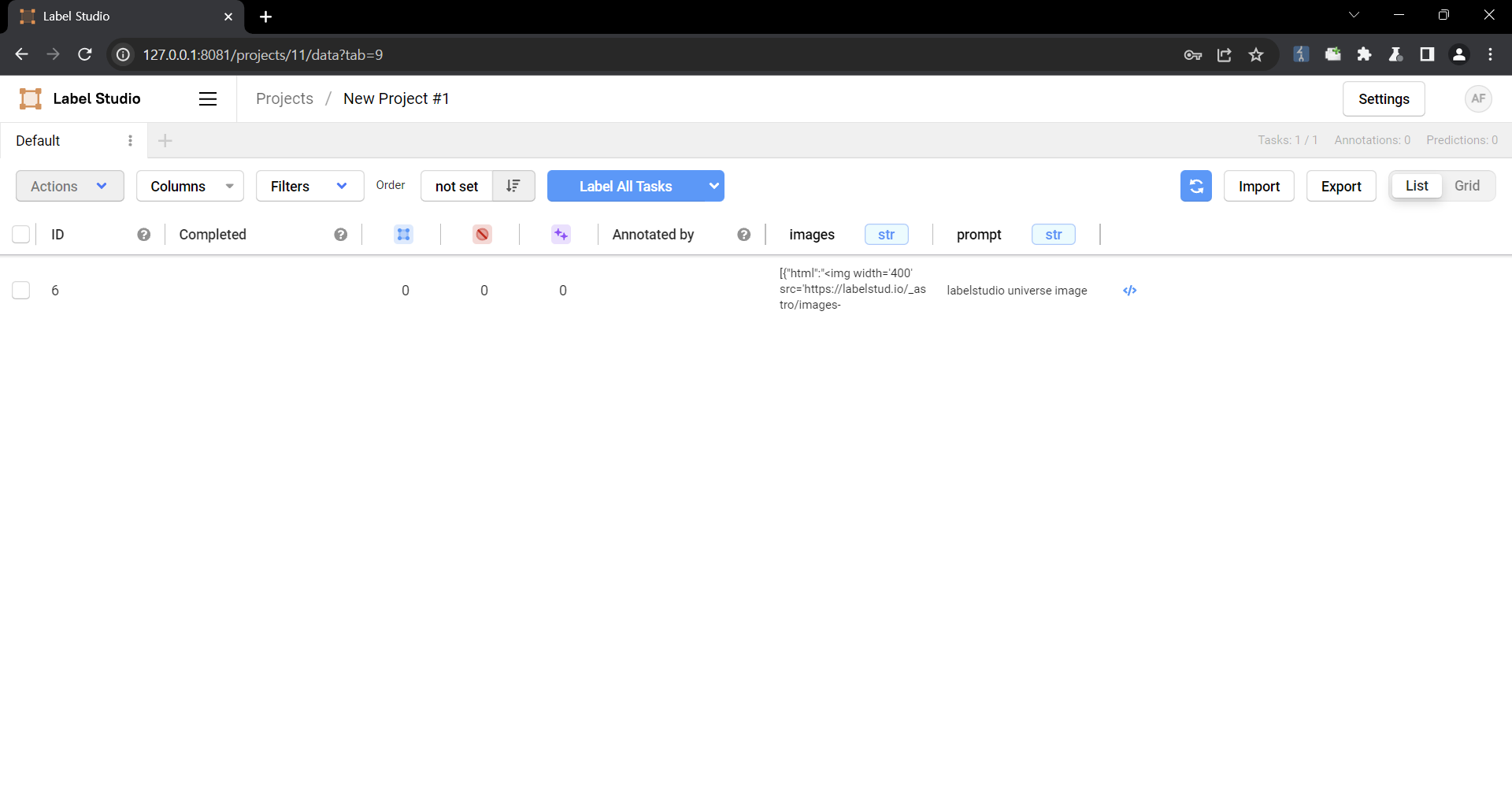\\n\\n5. Check that the script is running\\n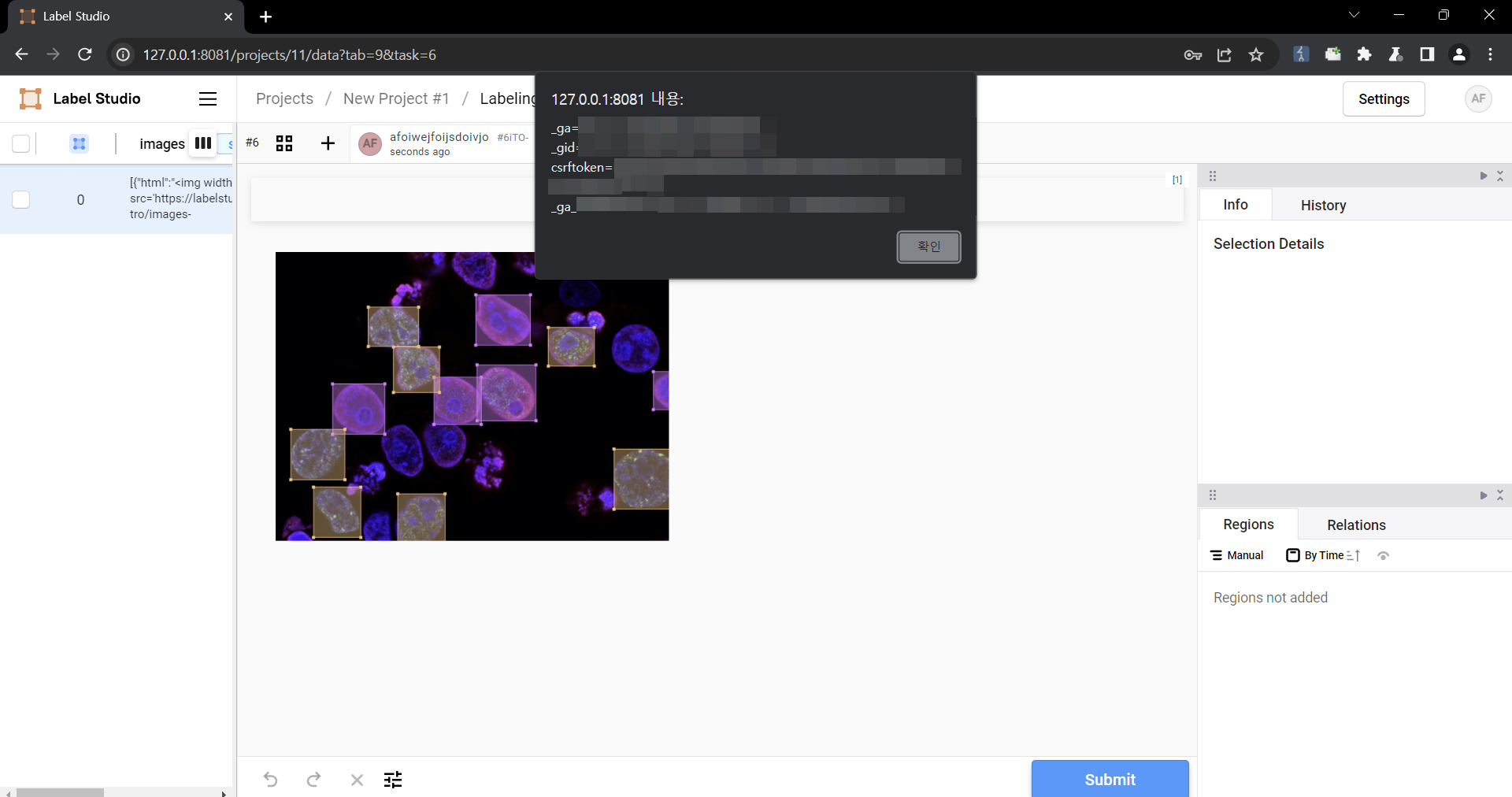\\n\\n### Impact\\nMalicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.\\n\"},{\"lang\":\"es\",\"value\":\"### Resumen En todas las versiones de Label Studio anteriores a la 1.11.0, los datos importados mediante la funci\u00f3n de carga de archivos no se desinfectan adecuadamente antes de procesarse dentro de [`Choices`](https://labelstud.io/tags/choices) o [`Labels`](https://labelstud.io/tags/labels), lo que genera una vulnerabilidad XSS. ### Detalles Necesita permiso para utilizar la funci\u00f3n \\\"importaci\u00f3n de datos\\\". Esto fue reproducido en Label Studio 1.10.1. ### PoC 1. Cree un proyecto.  2. Cargue un archivo que contenga la carga \u00fatil usando la funci\u00f3n \\\"Cargar archivos\\\" .   Los siguientes son los contenidos de los archivos utilizados en el PoC ``` { \\\"data\\\": { \\\" Prompt\\\": \\\"imagen del universo de labelstudio\\\", \\\"images\\\": [ { \\\"value\\\": \\\"id123#0\\\", \\\"style\\\": \\\"margin: 5px\\\", \\\"html\\\": \\\"\\\" } ] } } ``` 3. Seleccione la plantilla de etiquetado de generaci\u00f3n de texto a imagen de Clasificaci\u00f3n y puntuaci\u00f3n 4. \u00a1Seleccione una tarea! [4 Seleccione una tarea](https://github.com/HumanSignal/label-studio/assets/3943358/71856b7a-2b1f-44ea-99ab-fc48bc20caa7) 5. \u00a1Compruebe que el script se est\u00e9 ejecutando! [5 Compruebe que el script se est\u00e9 ejecutando](https://github.com/ HumanSignal/label-studio/assets/3943358/e396ae7b-a591-4db7-afe9-5bab30b48cb9) ### Impacto Se pueden inyectar scripts maliciosos en el c\u00f3digo y, cuando se vinculan con vulnerabilidades como CSRF, pueden causar un da\u00f1o a\u00fan mayor. En particular, puede convertirse en una fuente de nuevos ataques, especialmente cuando se vincula a la ingenier\u00eda social.\"}],\"metrics\":{\"cvssMetricV31\":[{\"source\":\"security-advisories@github.com\",\"type\":\"Secondary\",\"cvssData\":{\"version\":\"3.1\",\"vectorString\":\"CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N\",\"baseScore\":4.7,\"baseSeverity\":\"MEDIUM\",\"attackVector\":\"NETWORK\",\"attackComplexity\":\"LOW\",\"privilegesRequired\":\"NONE\",\"userInteraction\":\"REQUIRED\",\"scope\":\"CHANGED\",\"confidentialityImpact\":\"LOW\",\"integrityImpact\":\"NONE\",\"availabilityImpact\":\"NONE\"},\"exploitabilityScore\":2.8,\"impactScore\":1.4},{\"source\":\"nvd@nist.gov\",\"type\":\"Primary\",\"cvssData\":{\"version\":\"3.1\",\"vectorString\":\"CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N\",\"baseScore\":6.1,\"baseSeverity\":\"MEDIUM\",\"attackVector\":\"NETWORK\",\"attackComplexity\":\"LOW\",\"privilegesRequired\":\"NONE\",\"userInteraction\":\"REQUIRED\",\"scope\":\"CHANGED\",\"confidentialityImpact\":\"LOW\",\"integrityImpact\":\"LOW\",\"availabilityImpact\":\"NONE\"},\"exploitabilityScore\":2.8,\"impactScore\":2.7}]},\"weaknesses\":[{\"source\":\"security-advisories@github.com\",\"type\":\"Secondary\",\"description\":[{\"lang\":\"en\",\"value\":\"CWE-79\"}]},{\"source\":\"nvd@nist.gov\",\"type\":\"Primary\",\"description\":[{\"lang\":\"en\",\"value\":\"CWE-79\"}]}],\"configurations\":[{\"nodes\":[{\"operator\":\"OR\",\"negate\":false,\"cpeMatch\":[{\"vulnerable\":true,\"criteria\":\"cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:*\",\"versionEndExcluding\":\"1.11.0\",\"matchCriteriaId\":\"27567917-A7FB-4767-B9F6-6C8D422D62E7\"}]}]}],\"references\":[{\"url\":\"https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8\",\"source\":\"security-advisories@github.com\",\"tags\":[\"Patch\"]},{\"url\":\"https://github.com/HumanSignal/label-studio/pull/5232\",\"source\":\"security-advisories@github.com\",\"tags\":[\"Patch\"]},{\"url\":\"https://github.com/HumanSignal/label-studio/releases/tag/1.11.0\",\"source\":\"security-advisories@github.com\",\"tags\":[\"Release Notes\"]},{\"url\":\"https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg\",\"source\":\"security-advisories@github.com\",\"tags\":[\"Exploit\",\"Vendor Advisory\"]},{\"url\":\"https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8\",\"source\":\"af854a3a-2127-422b-91ae-364da2661108\",\"tags\":[\"Patch\"]},{\"url\":\"https://github.com/HumanSignal/label-studio/pull/5232\",\"source\":\"af854a3a-2127-422b-91ae-364da2661108\",\"tags\":[\"Patch\"]},{\"url\":\"https://github.com/HumanSignal/label-studio/releases/tag/1.11.0\",\"source\":\"af854a3a-2127-422b-91ae-364da2661108\",\"tags\":[\"Release Notes\"]},{\"url\":\"https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg\",\"source\":\"af854a3a-2127-422b-91ae-364da2661108\",\"tags\":[\"Exploit\",\"Vendor Advisory\"]}]}}",
"vulnrichment": {
"containers": "{\"adp\": [{\"title\": \"CVE Program Container\", \"references\": [{\"url\": \"https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg\", \"name\": \"https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg\", \"tags\": [\"x_refsource_CONFIRM\", \"x_transferred\"]}, {\"url\": \"https://github.com/HumanSignal/label-studio/pull/5232\", \"name\": \"https://github.com/HumanSignal/label-studio/pull/5232\", \"tags\": [\"x_refsource_MISC\", \"x_transferred\"]}, {\"url\": \"https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8\", \"name\": \"https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8\", \"tags\": [\"x_refsource_MISC\", \"x_transferred\"]}, {\"url\": \"https://github.com/HumanSignal/label-studio/releases/tag/1.11.0\", \"name\": \"https://github.com/HumanSignal/label-studio/releases/tag/1.11.0\", \"tags\": [\"x_refsource_MISC\", \"x_transferred\"]}], \"providerMetadata\": {\"orgId\": \"af854a3a-2127-422b-91ae-364da2661108\", \"shortName\": \"CVE\", \"dateUpdated\": \"2024-08-01T23:59:32.696Z\"}}, {\"title\": \"CISA ADP Vulnrichment\", \"metrics\": [{\"other\": {\"type\": \"ssvc\", \"content\": {\"id\": \"CVE-2024-26152\", \"role\": \"CISA Coordinator\", \"options\": [{\"Exploitation\": \"poc\"}, {\"Automatable\": \"no\"}, {\"Technical Impact\": \"partial\"}], \"version\": \"2.0.3\", \"timestamp\": \"2024-02-23T14:32:49.819252Z\"}}}], \"affected\": [{\"cpes\": [\"cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:*\"], \"vendor\": \"humansignal\", \"product\": \"label_studio\", \"versions\": [{\"status\": \"affected\", \"version\": \"0\", \"lessThan\": \"1.11.0\", \"versionType\": \"custom\"}], \"defaultStatus\": \"unknown\"}], \"providerMetadata\": {\"orgId\": \"134c704f-9b21-4f2e-91b3-4a467353bcc0\", \"shortName\": \"CISA-ADP\", \"dateUpdated\": \"2024-08-14T15:31:56.784Z\"}}], \"cna\": {\"title\": \"Label Studio vulnerable to Cross-site Scripting if `\u003cChoices\u003e` or `\u003cLabels\u003e` are used in labeling config \", \"source\": {\"advisory\": \"GHSA-6xv9-957j-qfhg\", \"discovery\": \"UNKNOWN\"}, \"metrics\": [{\"cvssV3_1\": {\"scope\": \"CHANGED\", \"version\": \"3.1\", \"baseScore\": 4.7, \"attackVector\": \"NETWORK\", \"baseSeverity\": \"MEDIUM\", \"vectorString\": \"CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N\", \"integrityImpact\": \"NONE\", \"userInteraction\": \"REQUIRED\", \"attackComplexity\": \"LOW\", \"availabilityImpact\": \"NONE\", \"privilegesRequired\": \"NONE\", \"confidentialityImpact\": \"LOW\"}}], \"affected\": [{\"vendor\": \"HumanSignal\", \"product\": \"label-studio\", \"versions\": [{\"status\": \"affected\", \"version\": \"\u003c 1.11.0\"}]}], \"references\": [{\"url\": \"https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg\", \"name\": \"https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg\", \"tags\": [\"x_refsource_CONFIRM\"]}, {\"url\": \"https://github.com/HumanSignal/label-studio/pull/5232\", \"name\": \"https://github.com/HumanSignal/label-studio/pull/5232\", \"tags\": [\"x_refsource_MISC\"]}, {\"url\": \"https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8\", \"name\": \"https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8\", \"tags\": [\"x_refsource_MISC\"]}, {\"url\": \"https://github.com/HumanSignal/label-studio/releases/tag/1.11.0\", \"name\": \"https://github.com/HumanSignal/label-studio/releases/tag/1.11.0\", \"tags\": [\"x_refsource_MISC\"]}], \"descriptions\": [{\"lang\": \"en\", \"value\": \"### Summary\\nOn all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.\\n\\n### Details\\nNeed permission to use the \\\"data import\\\" function. This was reproduced on Label Studio 1.10.1.\\n\\n### PoC\\n\\n1. Create a project.\\n\\n\\n2. Upload a file containing the payload using the \\\"Upload Files\\\" function.\\n\\n\\n\\nThe following are the contents of the files used in the PoC\\n```\\n{\\n \\\"data\\\": {\\n \\\"prompt\\\": \\\"labelstudio universe image\\\",\\n \\\"images\\\": [\\n {\\n \\\"value\\\": \\\"id123#0\\\",\\n \\\"style\\\": \\\"margin: 5px\\\",\\n \\\"html\\\": \\\"\u003cimg width=\u0027400\u0027 src=\u0027https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif\u0027 onload=alert(document.cookie)\u003e\\\"\\n }\\n ]\\n }\\n}\\n```\\n\\n3. Select the text-to-image generation labeling template of Ranking and scoring\\n\\n\\n\\n4. Select a task\\n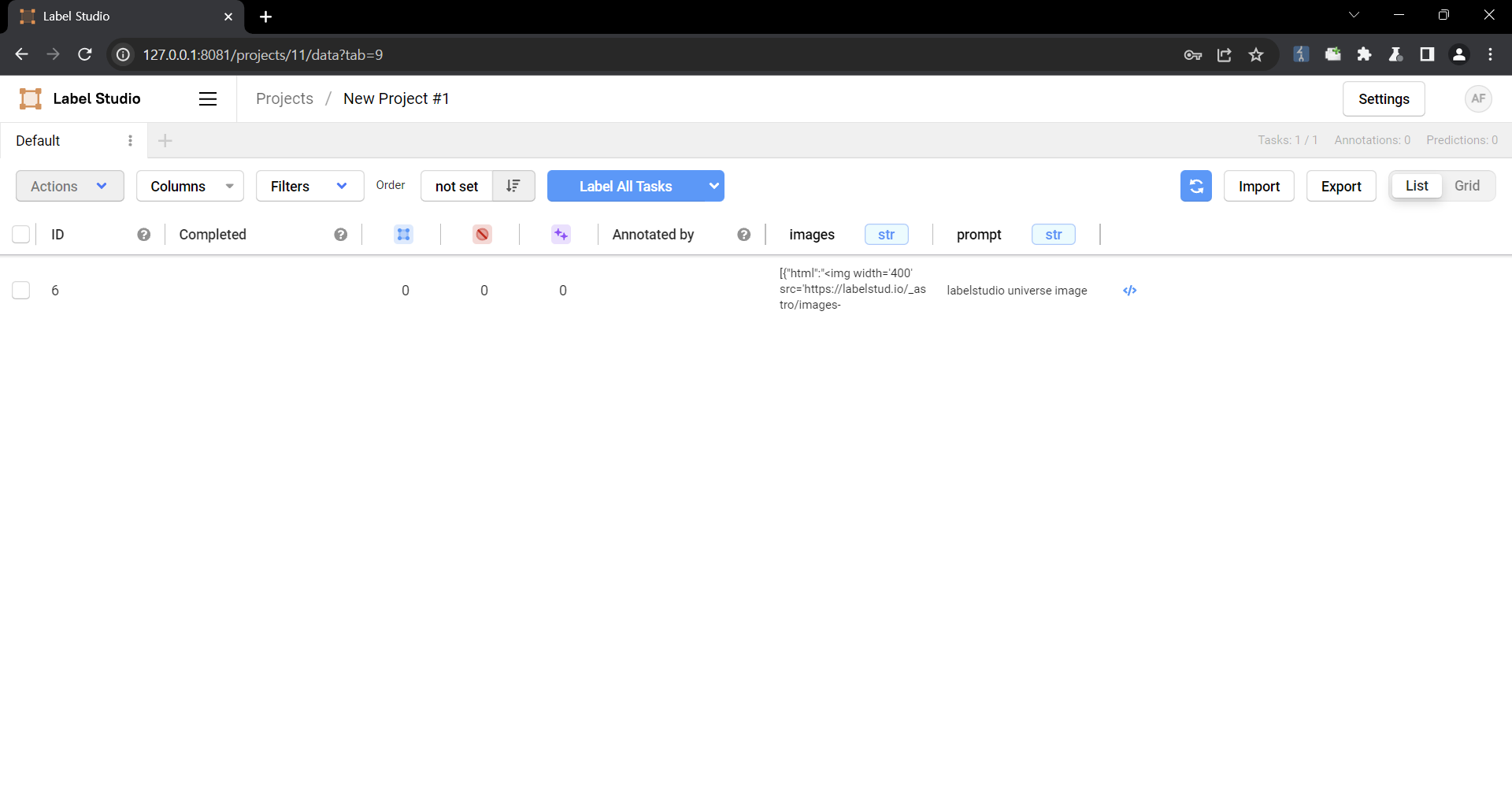\\n\\n5. Check that the script is running\\n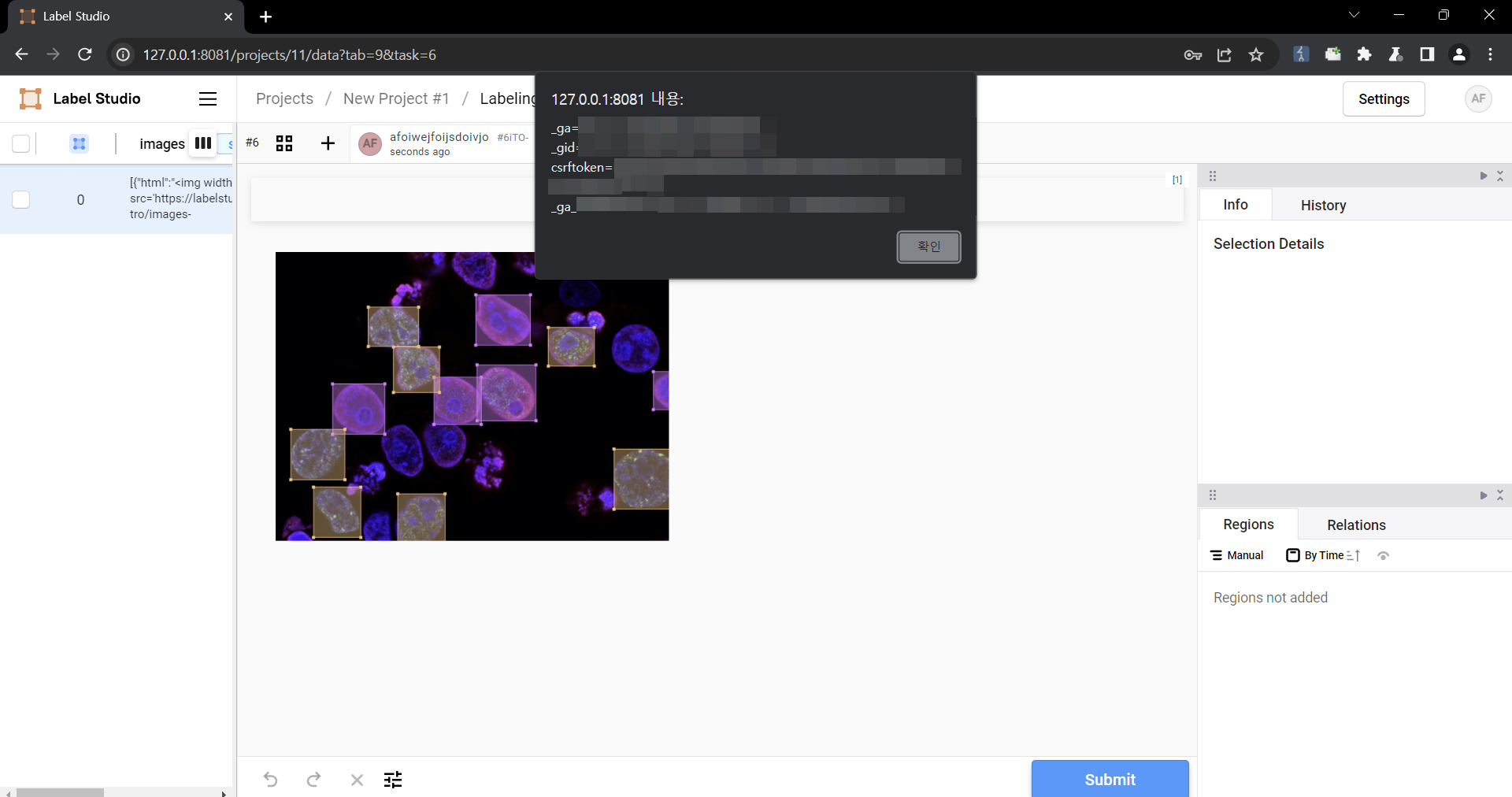\\n\\n### Impact\\nMalicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.\\n\"}], \"problemTypes\": [{\"descriptions\": [{\"lang\": \"en\", \"type\": \"CWE\", \"cweId\": \"CWE-79\", \"description\": \"CWE-79: Improper Neutralization of Input During Web Page Generation (\u0027Cross-site Scripting\u0027)\"}]}], \"providerMetadata\": {\"orgId\": \"a0819718-46f1-4df5-94e2-005712e83aaa\", \"shortName\": \"GitHub_M\", \"dateUpdated\": \"2024-02-22T21:52:26.193Z\"}}}",
"cveMetadata": "{\"cveId\": \"CVE-2024-26152\", \"state\": \"PUBLISHED\", \"dateUpdated\": \"2024-08-14T15:32:05.054Z\", \"dateReserved\": \"2024-02-14T17:40:03.690Z\", \"assignerOrgId\": \"a0819718-46f1-4df5-94e2-005712e83aaa\", \"datePublished\": \"2024-02-22T21:52:26.193Z\", \"assignerShortName\": \"GitHub_M\"}",
"dataType": "CVE_RECORD",
"dataVersion": "5.1"
}
}
}
Loading…
Loading…
Experimental. This forecast is provided for visualization only and may change without notice. Do not use it for operational decisions.
Forecast uses a logistic model when the trend is rising, or an exponential decay model when the trend is falling. Fitted via linearized least squares.
Sightings
| Author | Source | Type | Date | Other |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.
Loading…
Loading…