CVE-2023-27584 (GCVE-0-2023-27584)
Vulnerability from cvelistv5 – Published: 2024-09-19 22:54 – Updated: 2024-09-26 03:55
VLAI
Title
Dragonfly2 vulnerable to hard coded cyptographic key
Summary
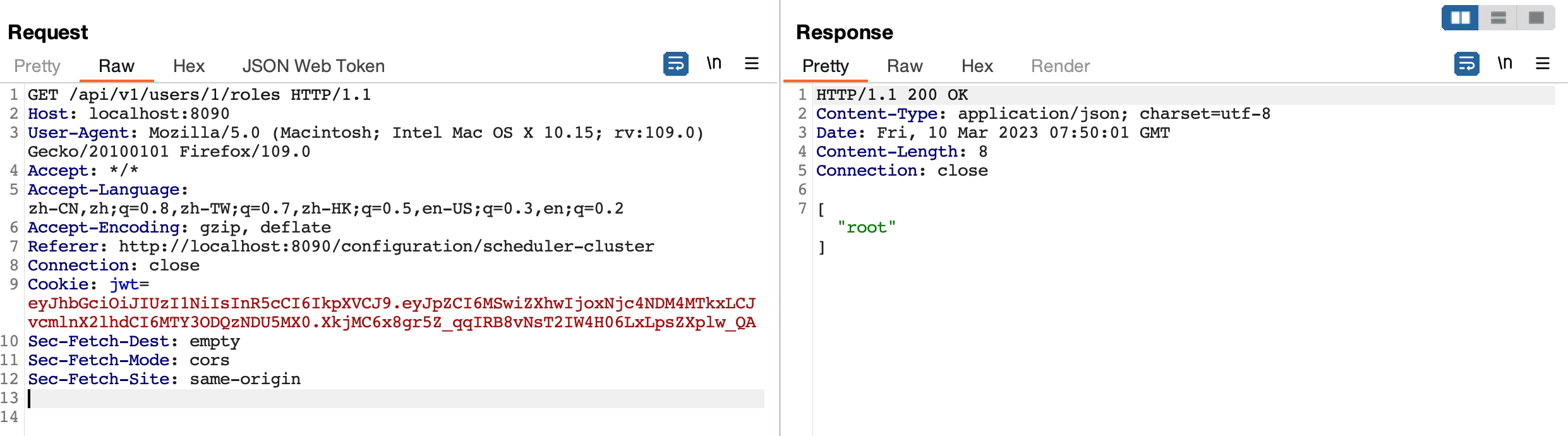
Dragonfly is an open source P2P-based file distribution and image acceleration system. It is hosted by the Cloud Native Computing Foundation (CNCF) as an Incubating Level Project. Dragonfly uses JWT to verify user. However, the secret key for JWT, "Secret Key", is hard coded, which leads to authentication bypass. An attacker can perform any action as a user with admin privileges. This issue has been addressed in release version 2.0.9. All users are advised to upgrade. There are no known workarounds for this vulnerability.
Severity
9.8 (Critical)
CWE
- CWE-321 - Use of Hard-coded Cryptographic Key
Assigner
References
2 references
| URL | Tags |
|---|---|
| https://github.com/dragonflyoss/Dragonfly2/securi… | x_refsource_CONFIRM |
| https://github.com/dragonflyoss/Dragonfly2/releas… | x_refsource_MISC |
Impacted products
1 product
| Vendor | Product | Version | |
|---|---|---|---|
| dragonflyoss | Dragonfly2 |
Affected:
< 2.0.9
|
{
"containers": {
"adp": [
{
"affected": [
{
"cpes": [
"cpe:2.3:a:dragonflyoss:dragonfly2:*:*:*:*:*:*:*:*"
],
"defaultStatus": "unknown",
"product": "dragonfly2",
"vendor": "dragonflyoss",
"versions": [
{
"lessThan": "2.0.9",
"status": "affected",
"version": "0",
"versionType": "custom"
}
]
}
],
"metrics": [
{
"other": {
"content": {
"id": "CVE-2023-27584",
"options": [
{
"Exploitation": "poc"
},
{
"Automatable": "yes"
},
{
"Technical Impact": "total"
}
],
"role": "CISA Coordinator",
"timestamp": "2024-09-25T00:00:00+00:00",
"version": "2.0.3"
},
"type": "ssvc"
}
}
],
"providerMetadata": {
"dateUpdated": "2024-09-26T03:55:52.647Z",
"orgId": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"shortName": "CISA-ADP"
},
"title": "CISA ADP Vulnrichment"
}
],
"cna": {
"affected": [
{
"product": "Dragonfly2",
"vendor": "dragonflyoss",
"versions": [
{
"status": "affected",
"version": "\u003c 2.0.9"
}
]
}
],
"descriptions": [
{
"lang": "en",
"value": "Dragonfly is an open source P2P-based file distribution and image acceleration system. It is hosted by the Cloud Native Computing Foundation (CNCF) as an Incubating Level Project. Dragonfly uses JWT to verify user. However, the secret key for JWT, \"Secret Key\", is hard coded, which leads to authentication bypass. An attacker can perform any action as a user with admin privileges. This issue has been addressed in release version 2.0.9. All users are advised to upgrade. There are no known workarounds for this vulnerability."
}
],
"metrics": [
{
"cvssV3_1": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
}
}
],
"problemTypes": [
{
"descriptions": [
{
"cweId": "CWE-321",
"description": "CWE-321: Use of Hard-coded Cryptographic Key",
"lang": "en",
"type": "CWE"
}
]
}
],
"providerMetadata": {
"dateUpdated": "2024-09-19T22:54:40.045Z",
"orgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"shortName": "GitHub_M"
},
"references": [
{
"name": "https://github.com/dragonflyoss/Dragonfly2/security/advisories/GHSA-hpc8-7wpm-889w",
"tags": [
"x_refsource_CONFIRM"
],
"url": "https://github.com/dragonflyoss/Dragonfly2/security/advisories/GHSA-hpc8-7wpm-889w"
},
{
"name": "https://github.com/dragonflyoss/Dragonfly2/releases/tag/v2.0.9",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/dragonflyoss/Dragonfly2/releases/tag/v2.0.9"
}
],
"source": {
"advisory": "GHSA-hpc8-7wpm-889w",
"discovery": "UNKNOWN"
},
"title": "Dragonfly2 vulnerable to hard coded cyptographic key"
}
},
"cveMetadata": {
"assignerOrgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"assignerShortName": "GitHub_M",
"cveId": "CVE-2023-27584",
"datePublished": "2024-09-19T22:54:40.045Z",
"dateReserved": "2023-03-04T01:03:53.634Z",
"dateUpdated": "2024-09-26T03:55:52.647Z",
"state": "PUBLISHED"
},
"dataType": "CVE_RECORD",
"dataVersion": "5.1",
"vulnerability-lookup:meta": {
"epss": {
"cve": "CVE-2023-27584",
"date": "2026-05-30",
"epss": "0.66176",
"percentile": "0.98541"
},
"fkie_nvd": {
"configurations": "[{\"nodes\": [{\"operator\": \"OR\", \"negate\": false, \"cpeMatch\": [{\"vulnerable\": true, \"criteria\": \"cpe:2.3:a:linuxfoundation:dragonfly:*:*:*:*:*:go:*:*\", \"versionEndExcluding\": \"2.0.9\", \"matchCriteriaId\": \"72F934F8-8793-41F8-9D9E-8D1B545683A6\"}]}]}]",
"descriptions": "[{\"lang\": \"en\", \"value\": \"Dragonfly is an open source P2P-based file distribution and image acceleration system. It is hosted by the Cloud Native Computing Foundation (CNCF) as an Incubating Level Project. Dragonfly uses JWT to verify user. However, the secret key for JWT, \\\"Secret Key\\\", is hard coded, which leads to authentication bypass. An attacker can perform any action as a user with admin privileges. This issue has been addressed in release version 2.0.9. All users are advised to upgrade. There are no known workarounds for this vulnerability.\"}, {\"lang\": \"es\", \"value\": \"Dragonfly es un sistema de distribuci\\u00f3n de archivos y aceleraci\\u00f3n de im\\u00e1genes basado en P2P de c\\u00f3digo abierto. Est\\u00e1 alojado por la Cloud Native Computing Foundation (CNCF) como un proyecto de nivel de incubaci\\u00f3n. Dragonfly utiliza JWT para verificar al usuario. Sin embargo, la clave secreta para JWT, \\\"Clave secreta\\\", est\\u00e1 codificada de forma r\\u00edgida, lo que permite eludir la autenticaci\\u00f3n. Un atacante puede realizar cualquier acci\\u00f3n como usuario con privilegios de administrador. Este problema se ha solucionado en la versi\\u00f3n 2.0.9. Se recomienda a todos los usuarios que actualicen. No existen workarounds conocidas para esta vulnerabilidad.\"}]",
"id": "CVE-2023-27584",
"lastModified": "2024-12-20T19:11:43.870",
"metrics": "{\"cvssMetricV31\": [{\"source\": \"security-advisories@github.com\", \"type\": \"Secondary\", \"cvssData\": {\"version\": \"3.1\", \"vectorString\": \"CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H\", \"baseScore\": 9.8, \"baseSeverity\": \"CRITICAL\", \"attackVector\": \"NETWORK\", \"attackComplexity\": \"LOW\", \"privilegesRequired\": \"NONE\", \"userInteraction\": \"NONE\", \"scope\": \"UNCHANGED\", \"confidentialityImpact\": \"HIGH\", \"integrityImpact\": \"HIGH\", \"availabilityImpact\": \"HIGH\"}, \"exploitabilityScore\": 3.9, \"impactScore\": 5.9}, {\"source\": \"nvd@nist.gov\", \"type\": \"Primary\", \"cvssData\": {\"version\": \"3.1\", \"vectorString\": \"CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H\", \"baseScore\": 9.8, \"baseSeverity\": \"CRITICAL\", \"attackVector\": \"NETWORK\", \"attackComplexity\": \"LOW\", \"privilegesRequired\": \"NONE\", \"userInteraction\": \"NONE\", \"scope\": \"UNCHANGED\", \"confidentialityImpact\": \"HIGH\", \"integrityImpact\": \"HIGH\", \"availabilityImpact\": \"HIGH\"}, \"exploitabilityScore\": 3.9, \"impactScore\": 5.9}]}",
"published": "2024-09-19T23:15:11.233",
"references": "[{\"url\": \"https://github.com/dragonflyoss/Dragonfly2/releases/tag/v2.0.9\", \"source\": \"security-advisories@github.com\", \"tags\": [\"Release Notes\"]}, {\"url\": \"https://github.com/dragonflyoss/Dragonfly2/security/advisories/GHSA-hpc8-7wpm-889w\", \"source\": \"security-advisories@github.com\", \"tags\": [\"Exploit\", \"Vendor Advisory\"]}]",
"sourceIdentifier": "security-advisories@github.com",
"vulnStatus": "Analyzed",
"weaknesses": "[{\"source\": \"security-advisories@github.com\", \"type\": \"Secondary\", \"description\": [{\"lang\": \"en\", \"value\": \"CWE-321\"}]}, {\"source\": \"nvd@nist.gov\", \"type\": \"Primary\", \"description\": [{\"lang\": \"en\", \"value\": \"CWE-798\"}]}]"
},
"nvd": "{\"cve\":{\"id\":\"CVE-2023-27584\",\"sourceIdentifier\":\"security-advisories@github.com\",\"published\":\"2024-09-19T23:15:11.233\",\"lastModified\":\"2024-12-20T19:11:43.870\",\"vulnStatus\":\"Analyzed\",\"cveTags\":[],\"descriptions\":[{\"lang\":\"en\",\"value\":\"Dragonfly is an open source P2P-based file distribution and image acceleration system. It is hosted by the Cloud Native Computing Foundation (CNCF) as an Incubating Level Project. Dragonfly uses JWT to verify user. However, the secret key for JWT, \\\"Secret Key\\\", is hard coded, which leads to authentication bypass. An attacker can perform any action as a user with admin privileges. This issue has been addressed in release version 2.0.9. All users are advised to upgrade. There are no known workarounds for this vulnerability.\"},{\"lang\":\"es\",\"value\":\"Dragonfly es un sistema de distribuci\u00f3n de archivos y aceleraci\u00f3n de im\u00e1genes basado en P2P de c\u00f3digo abierto. Est\u00e1 alojado por la Cloud Native Computing Foundation (CNCF) como un proyecto de nivel de incubaci\u00f3n. Dragonfly utiliza JWT para verificar al usuario. Sin embargo, la clave secreta para JWT, \\\"Clave secreta\\\", est\u00e1 codificada de forma r\u00edgida, lo que permite eludir la autenticaci\u00f3n. Un atacante puede realizar cualquier acci\u00f3n como usuario con privilegios de administrador. Este problema se ha solucionado en la versi\u00f3n 2.0.9. Se recomienda a todos los usuarios que actualicen. No existen workarounds conocidas para esta vulnerabilidad.\"}],\"metrics\":{\"cvssMetricV31\":[{\"source\":\"security-advisories@github.com\",\"type\":\"Secondary\",\"cvssData\":{\"version\":\"3.1\",\"vectorString\":\"CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H\",\"baseScore\":9.8,\"baseSeverity\":\"CRITICAL\",\"attackVector\":\"NETWORK\",\"attackComplexity\":\"LOW\",\"privilegesRequired\":\"NONE\",\"userInteraction\":\"NONE\",\"scope\":\"UNCHANGED\",\"confidentialityImpact\":\"HIGH\",\"integrityImpact\":\"HIGH\",\"availabilityImpact\":\"HIGH\"},\"exploitabilityScore\":3.9,\"impactScore\":5.9},{\"source\":\"nvd@nist.gov\",\"type\":\"Primary\",\"cvssData\":{\"version\":\"3.1\",\"vectorString\":\"CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H\",\"baseScore\":9.8,\"baseSeverity\":\"CRITICAL\",\"attackVector\":\"NETWORK\",\"attackComplexity\":\"LOW\",\"privilegesRequired\":\"NONE\",\"userInteraction\":\"NONE\",\"scope\":\"UNCHANGED\",\"confidentialityImpact\":\"HIGH\",\"integrityImpact\":\"HIGH\",\"availabilityImpact\":\"HIGH\"},\"exploitabilityScore\":3.9,\"impactScore\":5.9}]},\"weaknesses\":[{\"source\":\"security-advisories@github.com\",\"type\":\"Secondary\",\"description\":[{\"lang\":\"en\",\"value\":\"CWE-321\"}]},{\"source\":\"nvd@nist.gov\",\"type\":\"Primary\",\"description\":[{\"lang\":\"en\",\"value\":\"CWE-798\"}]}],\"configurations\":[{\"nodes\":[{\"operator\":\"OR\",\"negate\":false,\"cpeMatch\":[{\"vulnerable\":true,\"criteria\":\"cpe:2.3:a:linuxfoundation:dragonfly:*:*:*:*:*:go:*:*\",\"versionEndExcluding\":\"2.0.9\",\"matchCriteriaId\":\"72F934F8-8793-41F8-9D9E-8D1B545683A6\"}]}]}],\"references\":[{\"url\":\"https://github.com/dragonflyoss/Dragonfly2/releases/tag/v2.0.9\",\"source\":\"security-advisories@github.com\",\"tags\":[\"Release Notes\"]},{\"url\":\"https://github.com/dragonflyoss/Dragonfly2/security/advisories/GHSA-hpc8-7wpm-889w\",\"source\":\"security-advisories@github.com\",\"tags\":[\"Exploit\",\"Vendor Advisory\"]}]}}",
"vulnrichment": {
"containers": "{\"adp\": [{\"title\": \"CISA ADP Vulnrichment\", \"metrics\": [{\"other\": {\"type\": \"ssvc\", \"content\": {\"id\": \"CVE-2023-27584\", \"role\": \"CISA Coordinator\", \"options\": [{\"Exploitation\": \"poc\"}, {\"Automatable\": \"yes\"}, {\"Technical Impact\": \"total\"}], \"version\": \"2.0.3\", \"timestamp\": \"2024-09-20T15:16:05.941246Z\"}}}], \"affected\": [{\"cpes\": [\"cpe:2.3:a:dragonflyoss:dragonfly2:*:*:*:*:*:*:*:*\"], \"vendor\": \"dragonflyoss\", \"product\": \"dragonfly2\", \"versions\": [{\"status\": \"affected\", \"version\": \"0\", \"lessThan\": \"2.0.9\", \"versionType\": \"custom\"}], \"defaultStatus\": \"unknown\"}], \"providerMetadata\": {\"orgId\": \"134c704f-9b21-4f2e-91b3-4a467353bcc0\", \"shortName\": \"CISA-ADP\", \"dateUpdated\": \"2024-09-20T15:20:30.612Z\"}}], \"cna\": {\"title\": \"Dragonfly2 vulnerable to hard coded cyptographic key\", \"source\": {\"advisory\": \"GHSA-hpc8-7wpm-889w\", \"discovery\": \"UNKNOWN\"}, \"metrics\": [{\"cvssV3_1\": {\"scope\": \"UNCHANGED\", \"version\": \"3.1\", \"baseScore\": 9.8, \"attackVector\": \"NETWORK\", \"baseSeverity\": \"CRITICAL\", \"vectorString\": \"CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H\", \"integrityImpact\": \"HIGH\", \"userInteraction\": \"NONE\", \"attackComplexity\": \"LOW\", \"availabilityImpact\": \"HIGH\", \"privilegesRequired\": \"NONE\", \"confidentialityImpact\": \"HIGH\"}}], \"affected\": [{\"vendor\": \"dragonflyoss\", \"product\": \"Dragonfly2\", \"versions\": [{\"status\": \"affected\", \"version\": \"\u003c 2.0.9\"}]}], \"references\": [{\"url\": \"https://github.com/dragonflyoss/Dragonfly2/security/advisories/GHSA-hpc8-7wpm-889w\", \"name\": \"https://github.com/dragonflyoss/Dragonfly2/security/advisories/GHSA-hpc8-7wpm-889w\", \"tags\": [\"x_refsource_CONFIRM\"]}, {\"url\": \"https://github.com/dragonflyoss/Dragonfly2/releases/tag/v2.0.9\", \"name\": \"https://github.com/dragonflyoss/Dragonfly2/releases/tag/v2.0.9\", \"tags\": [\"x_refsource_MISC\"]}], \"descriptions\": [{\"lang\": \"en\", \"value\": \"Dragonfly is an open source P2P-based file distribution and image acceleration system. It is hosted by the Cloud Native Computing Foundation (CNCF) as an Incubating Level Project. Dragonfly uses JWT to verify user. However, the secret key for JWT, \\\"Secret Key\\\", is hard coded, which leads to authentication bypass. An attacker can perform any action as a user with admin privileges. This issue has been addressed in release version 2.0.9. All users are advised to upgrade. There are no known workarounds for this vulnerability.\"}], \"problemTypes\": [{\"descriptions\": [{\"lang\": \"en\", \"type\": \"CWE\", \"cweId\": \"CWE-321\", \"description\": \"CWE-321: Use of Hard-coded Cryptographic Key\"}]}], \"providerMetadata\": {\"orgId\": \"a0819718-46f1-4df5-94e2-005712e83aaa\", \"shortName\": \"GitHub_M\", \"dateUpdated\": \"2024-09-19T22:54:40.045Z\"}}}",
"cveMetadata": "{\"cveId\": \"CVE-2023-27584\", \"state\": \"PUBLISHED\", \"dateUpdated\": \"2024-09-26T03:55:52.647Z\", \"dateReserved\": \"2023-03-04T01:03:53.634Z\", \"assignerOrgId\": \"a0819718-46f1-4df5-94e2-005712e83aaa\", \"datePublished\": \"2024-09-19T22:54:40.045Z\", \"assignerShortName\": \"GitHub_M\"}",
"dataType": "CVE_RECORD",
"dataVersion": "5.1"
}
}
}
Loading…
Loading…
Experimental. This forecast is provided for visualization only and may change without notice. Do not use it for operational decisions.
Forecast uses a logistic model when the trend is rising, or an exponential decay model when the trend is falling. Fitted via linearized least squares.
Sightings
| Author | Source | Type | Date | Other |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.
Loading…
Loading…