CVE-2023-49276 (GCVE-0-2023-49276)
Vulnerability from cvelistv5 – Published: 2023-12-01 22:05 – Updated: 2024-08-02 21:53
VLAI
Title
Attribute Injection leading to XSS(Cross-Site-Scripting) in uptime-kuma
Summary
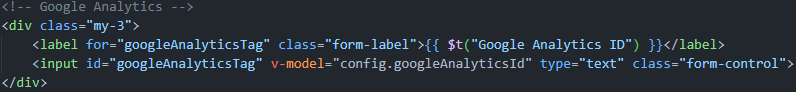
Uptime Kuma is an open source self-hosted monitoring tool. In affected versions the Google Analytics element in vulnerable to Attribute Injection leading to Cross-Site-Scripting (XSS). Since the custom status interface can set an independent Google Analytics ID and the template has not been sanitized, there is an attribute injection vulnerability here, which can lead to XSS attacks. This vulnerability has been addressed in commit `f28dccf4e` which is included in release version 1.23.7. Users are advised to upgrade. There are no known workarounds for this vulnerability.
Severity
6.3 (Medium)
CWE
- CWE-79 - Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')
Assigner
References
2 references
| URL | Tags |
|---|---|
| https://github.com/louislam/uptime-kuma/security/… | x_refsource_CONFIRM |
| https://github.com/louislam/uptime-kuma/commit/f2… | x_refsource_MISC |
Impacted products
1 product
| Vendor | Product | Version | |
|---|---|---|---|
| louislam | uptime-kuma |
Affected:
>= 1.20.0, < 1.23.7
|
{
"containers": {
"adp": [
{
"providerMetadata": {
"dateUpdated": "2024-08-02T21:53:44.985Z",
"orgId": "af854a3a-2127-422b-91ae-364da2661108",
"shortName": "CVE"
},
"references": [
{
"name": "https://github.com/louislam/uptime-kuma/security/advisories/GHSA-v4v2-8h88-65qj",
"tags": [
"x_refsource_CONFIRM",
"x_transferred"
],
"url": "https://github.com/louislam/uptime-kuma/security/advisories/GHSA-v4v2-8h88-65qj"
},
{
"name": "https://github.com/louislam/uptime-kuma/commit/f28dccf4e11f041564293e4f407e69ab9ee2277f",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/louislam/uptime-kuma/commit/f28dccf4e11f041564293e4f407e69ab9ee2277f"
}
],
"title": "CVE Program Container"
}
],
"cna": {
"affected": [
{
"product": "uptime-kuma",
"vendor": "louislam",
"versions": [
{
"status": "affected",
"version": "\u003e= 1.20.0, \u003c 1.23.7"
}
]
}
],
"descriptions": [
{
"lang": "en",
"value": "Uptime Kuma is an open source self-hosted monitoring tool. In affected versions the Google Analytics element in vulnerable to Attribute Injection leading to Cross-Site-Scripting (XSS). Since the custom status interface can set an independent Google Analytics ID and the template has not been sanitized, there is an attribute injection vulnerability here, which can lead to XSS attacks. This vulnerability has been addressed in commit `f28dccf4e` which is included in release version 1.23.7. Users are advised to upgrade. There are no known workarounds for this vulnerability."
}
],
"metrics": [
{
"cvssV3_1": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "HIGH",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:L/I:H/A:N",
"version": "3.1"
}
}
],
"problemTypes": [
{
"descriptions": [
{
"cweId": "CWE-79",
"description": "CWE-79: Improper Neutralization of Input During Web Page Generation (\u0027Cross-site Scripting\u0027)",
"lang": "en",
"type": "CWE"
}
]
}
],
"providerMetadata": {
"dateUpdated": "2023-12-01T22:05:41.789Z",
"orgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"shortName": "GitHub_M"
},
"references": [
{
"name": "https://github.com/louislam/uptime-kuma/security/advisories/GHSA-v4v2-8h88-65qj",
"tags": [
"x_refsource_CONFIRM"
],
"url": "https://github.com/louislam/uptime-kuma/security/advisories/GHSA-v4v2-8h88-65qj"
},
{
"name": "https://github.com/louislam/uptime-kuma/commit/f28dccf4e11f041564293e4f407e69ab9ee2277f",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/louislam/uptime-kuma/commit/f28dccf4e11f041564293e4f407e69ab9ee2277f"
}
],
"source": {
"advisory": "GHSA-v4v2-8h88-65qj",
"discovery": "UNKNOWN"
},
"title": "Attribute Injection leading to XSS(Cross-Site-Scripting) in uptime-kuma"
}
},
"cveMetadata": {
"assignerOrgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"assignerShortName": "GitHub_M",
"cveId": "CVE-2023-49276",
"datePublished": "2023-12-01T22:05:41.789Z",
"dateReserved": "2023-11-24T16:45:24.311Z",
"dateUpdated": "2024-08-02T21:53:44.985Z",
"state": "PUBLISHED"
},
"dataType": "CVE_RECORD",
"dataVersion": "5.1",
"vulnerability-lookup:meta": {
"epss": {
"cve": "CVE-2023-49276",
"date": "2026-05-27",
"epss": "0.00525",
"percentile": "0.67173"
},
"fkie_nvd": {
"configurations": "[{\"nodes\": [{\"operator\": \"OR\", \"negate\": false, \"cpeMatch\": [{\"vulnerable\": true, \"criteria\": \"cpe:2.3:a:uptime.kuma:uptime_kuma:*:*:*:*:*:*:*:*\", \"versionStartIncluding\": \"1.20.0\", \"versionEndExcluding\": \"1.23.7\", \"matchCriteriaId\": \"738D525E-0E73-4F2D-BFE6-47646D61CD65\"}]}]}]",
"descriptions": "[{\"lang\": \"en\", \"value\": \"Uptime Kuma is an open source self-hosted monitoring tool. In affected versions the Google Analytics element in vulnerable to Attribute Injection leading to Cross-Site-Scripting (XSS). Since the custom status interface can set an independent Google Analytics ID and the template has not been sanitized, there is an attribute injection vulnerability here, which can lead to XSS attacks. This vulnerability has been addressed in commit `f28dccf4e` which is included in release version 1.23.7. Users are advised to upgrade. There are no known workarounds for this vulnerability.\"}, {\"lang\": \"es\", \"value\": \"Uptime Kuma es una herramienta de monitoreo autohospedada de c\\u00f3digo abierto. En las versiones afectadas, el elemento Google Analytics es vulnerable a la inyecci\\u00f3n de atributos que conduce a Cross-Site-Scripting (XSS). Dado que la interfaz de estado personalizada puede establecer un ID de Google Analytics independiente y la plantilla no ha sido sanitizada, aqu\\u00ed existe una vulnerabilidad de inyecci\\u00f3n de atributos, que puede provocar ataques XSS. Esta vulnerabilidad se ha solucionado en el commit `f28dccf4e` que se incluye en la versi\\u00f3n 1.23.7. Se recomienda a los usuarios que actualicen. No se conocen workarounds para esta vulnerabilidad.\"}]",
"id": "CVE-2023-49276",
"lastModified": "2024-11-21T08:33:10.040",
"metrics": "{\"cvssMetricV31\": [{\"source\": \"security-advisories@github.com\", \"type\": \"Secondary\", \"cvssData\": {\"version\": \"3.1\", \"vectorString\": \"CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:L/I:H/A:N\", \"baseScore\": 6.3, \"baseSeverity\": \"MEDIUM\", \"attackVector\": \"NETWORK\", \"attackComplexity\": \"LOW\", \"privilegesRequired\": \"LOW\", \"userInteraction\": \"REQUIRED\", \"scope\": \"UNCHANGED\", \"confidentialityImpact\": \"LOW\", \"integrityImpact\": \"HIGH\", \"availabilityImpact\": \"NONE\"}, \"exploitabilityScore\": 2.1, \"impactScore\": 4.2}, {\"source\": \"nvd@nist.gov\", \"type\": \"Primary\", \"cvssData\": {\"version\": \"3.1\", \"vectorString\": \"CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N\", \"baseScore\": 6.1, \"baseSeverity\": \"MEDIUM\", \"attackVector\": \"NETWORK\", \"attackComplexity\": \"LOW\", \"privilegesRequired\": \"NONE\", \"userInteraction\": \"REQUIRED\", \"scope\": \"CHANGED\", \"confidentialityImpact\": \"LOW\", \"integrityImpact\": \"LOW\", \"availabilityImpact\": \"NONE\"}, \"exploitabilityScore\": 2.8, \"impactScore\": 2.7}]}",
"published": "2023-12-01T22:15:10.563",
"references": "[{\"url\": \"https://github.com/louislam/uptime-kuma/commit/f28dccf4e11f041564293e4f407e69ab9ee2277f\", \"source\": \"security-advisories@github.com\", \"tags\": [\"Patch\"]}, {\"url\": \"https://github.com/louislam/uptime-kuma/security/advisories/GHSA-v4v2-8h88-65qj\", \"source\": \"security-advisories@github.com\", \"tags\": [\"Exploit\", \"Vendor Advisory\"]}, {\"url\": \"https://github.com/louislam/uptime-kuma/commit/f28dccf4e11f041564293e4f407e69ab9ee2277f\", \"source\": \"af854a3a-2127-422b-91ae-364da2661108\", \"tags\": [\"Patch\"]}, {\"url\": \"https://github.com/louislam/uptime-kuma/security/advisories/GHSA-v4v2-8h88-65qj\", \"source\": \"af854a3a-2127-422b-91ae-364da2661108\", \"tags\": [\"Exploit\", \"Vendor Advisory\"]}]",
"sourceIdentifier": "security-advisories@github.com",
"vulnStatus": "Modified",
"weaknesses": "[{\"source\": \"security-advisories@github.com\", \"type\": \"Primary\", \"description\": [{\"lang\": \"en\", \"value\": \"CWE-79\"}]}]"
},
"nvd": "{\"cve\":{\"id\":\"CVE-2023-49276\",\"sourceIdentifier\":\"security-advisories@github.com\",\"published\":\"2023-12-01T22:15:10.563\",\"lastModified\":\"2024-11-21T08:33:10.040\",\"vulnStatus\":\"Modified\",\"cveTags\":[],\"descriptions\":[{\"lang\":\"en\",\"value\":\"Uptime Kuma is an open source self-hosted monitoring tool. In affected versions the Google Analytics element in vulnerable to Attribute Injection leading to Cross-Site-Scripting (XSS). Since the custom status interface can set an independent Google Analytics ID and the template has not been sanitized, there is an attribute injection vulnerability here, which can lead to XSS attacks. This vulnerability has been addressed in commit `f28dccf4e` which is included in release version 1.23.7. Users are advised to upgrade. There are no known workarounds for this vulnerability.\"},{\"lang\":\"es\",\"value\":\"Uptime Kuma es una herramienta de monitoreo autohospedada de c\u00f3digo abierto. En las versiones afectadas, el elemento Google Analytics es vulnerable a la inyecci\u00f3n de atributos que conduce a Cross-Site-Scripting (XSS). Dado que la interfaz de estado personalizada puede establecer un ID de Google Analytics independiente y la plantilla no ha sido sanitizada, aqu\u00ed existe una vulnerabilidad de inyecci\u00f3n de atributos, que puede provocar ataques XSS. Esta vulnerabilidad se ha solucionado en el commit `f28dccf4e` que se incluye en la versi\u00f3n 1.23.7. Se recomienda a los usuarios que actualicen. No se conocen workarounds para esta vulnerabilidad.\"}],\"metrics\":{\"cvssMetricV31\":[{\"source\":\"security-advisories@github.com\",\"type\":\"Secondary\",\"cvssData\":{\"version\":\"3.1\",\"vectorString\":\"CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:L/I:H/A:N\",\"baseScore\":6.3,\"baseSeverity\":\"MEDIUM\",\"attackVector\":\"NETWORK\",\"attackComplexity\":\"LOW\",\"privilegesRequired\":\"LOW\",\"userInteraction\":\"REQUIRED\",\"scope\":\"UNCHANGED\",\"confidentialityImpact\":\"LOW\",\"integrityImpact\":\"HIGH\",\"availabilityImpact\":\"NONE\"},\"exploitabilityScore\":2.1,\"impactScore\":4.2},{\"source\":\"nvd@nist.gov\",\"type\":\"Primary\",\"cvssData\":{\"version\":\"3.1\",\"vectorString\":\"CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N\",\"baseScore\":6.1,\"baseSeverity\":\"MEDIUM\",\"attackVector\":\"NETWORK\",\"attackComplexity\":\"LOW\",\"privilegesRequired\":\"NONE\",\"userInteraction\":\"REQUIRED\",\"scope\":\"CHANGED\",\"confidentialityImpact\":\"LOW\",\"integrityImpact\":\"LOW\",\"availabilityImpact\":\"NONE\"},\"exploitabilityScore\":2.8,\"impactScore\":2.7}]},\"weaknesses\":[{\"source\":\"security-advisories@github.com\",\"type\":\"Primary\",\"description\":[{\"lang\":\"en\",\"value\":\"CWE-79\"}]}],\"configurations\":[{\"nodes\":[{\"operator\":\"OR\",\"negate\":false,\"cpeMatch\":[{\"vulnerable\":true,\"criteria\":\"cpe:2.3:a:uptime.kuma:uptime_kuma:*:*:*:*:*:*:*:*\",\"versionStartIncluding\":\"1.20.0\",\"versionEndExcluding\":\"1.23.7\",\"matchCriteriaId\":\"738D525E-0E73-4F2D-BFE6-47646D61CD65\"}]}]}],\"references\":[{\"url\":\"https://github.com/louislam/uptime-kuma/commit/f28dccf4e11f041564293e4f407e69ab9ee2277f\",\"source\":\"security-advisories@github.com\",\"tags\":[\"Patch\"]},{\"url\":\"https://github.com/louislam/uptime-kuma/security/advisories/GHSA-v4v2-8h88-65qj\",\"source\":\"security-advisories@github.com\",\"tags\":[\"Exploit\",\"Vendor Advisory\"]},{\"url\":\"https://github.com/louislam/uptime-kuma/commit/f28dccf4e11f041564293e4f407e69ab9ee2277f\",\"source\":\"af854a3a-2127-422b-91ae-364da2661108\",\"tags\":[\"Patch\"]},{\"url\":\"https://github.com/louislam/uptime-kuma/security/advisories/GHSA-v4v2-8h88-65qj\",\"source\":\"af854a3a-2127-422b-91ae-364da2661108\",\"tags\":[\"Exploit\",\"Vendor Advisory\"]}]}}"
}
}
Loading…
Loading…
Experimental. This forecast is provided for visualization only and may change without notice. Do not use it for operational decisions.
Forecast uses a logistic model when the trend is rising, or an exponential decay model when the trend is falling. Fitted via linearized least squares.
Sightings
| Author | Source | Type | Date | Other |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.
Loading…
Loading…