GHSA-V4V2-8H88-65QJ
Vulnerability from github – Published: 2023-11-24 16:54 – Updated: 2023-12-07 22:59
VLAI
Summary
Attribute Injection leading to XSS(Cross-Site-Scripting)
Details
Summary
Google Analytics element Attribute Injection leading to XSS
Details
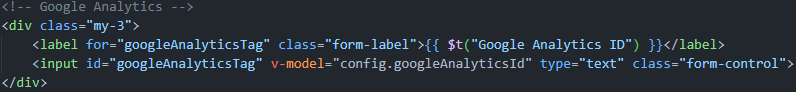
Since the custom status interface can set an independent Google Analytics ID and the template has not been sanitized, there is an attribute injection vulnerability here, which can lead to XSS attacks.
PoC
- Run the latest version of the louislam/uptime-kuma container and initialize the account password.
- Create a new status page.
- Edit the status page and change the Google Analytics ID to following payload(it only works for firefox. Any attribute can be injected, but this seems the most intuitive):
123123" onafterscriptexecute=alert(window.name+1),eval(window.name) a="x
- Click Save and return to the interface. XSS occurs.
screenshots:


Severity
6.1 (Medium)
{
"affected": [
{
"database_specific": {
"last_known_affected_version_range": "\u003c= 1.23.6"
},
"package": {
"ecosystem": "npm",
"name": "uptime-kuma"
},
"ranges": [
{
"events": [
{
"introduced": "1.20.0"
},
{
"fixed": "1.23.7"
}
],
"type": "ECOSYSTEM"
}
]
}
],
"aliases": [
"CVE-2023-49276"
],
"database_specific": {
"cwe_ids": [
"CWE-79"
],
"github_reviewed": true,
"github_reviewed_at": "2023-11-24T16:54:20Z",
"nvd_published_at": "2023-12-01T22:15:10Z",
"severity": "MODERATE"
},
"details": "### Summary\nGoogle Analytics element Attribute Injection leading to XSS\n\n### Details\nSince the custom status interface can set an independent Google Analytics ID and the template has not been sanitized, there is an attribute injection vulnerability here, which can lead to XSS attacks.\n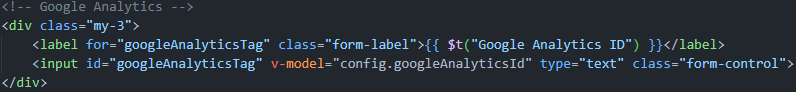\n\n### PoC\n1. Run the latest version of the louislam/uptime-kuma container and initialize the account password.\n2. Create a new status page.\n3. Edit the status page and change the Google Analytics ID to following payload(it only works for firefox. Any attribute can be injected, but this seems the most intuitive):\n```\n123123\" onafterscriptexecute=alert(window.name+1),eval(window.name) a=\"x\n```\n\n4. Click Save and return to the interface. XSS occurs.\nscreenshots:\n\n\n\n\n\n",
"id": "GHSA-v4v2-8h88-65qj",
"modified": "2023-12-07T22:59:07Z",
"published": "2023-11-24T16:54:20Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/louislam/uptime-kuma/security/advisories/GHSA-v4v2-8h88-65qj"
},
{
"type": "ADVISORY",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2023-49276"
},
{
"type": "WEB",
"url": "https://github.com/louislam/uptime-kuma/commit/f28dccf4e11f041564293e4f407e69ab9ee2277f"
},
{
"type": "PACKAGE",
"url": "https://github.com/louislam/uptime-kuma"
}
],
"schema_version": "1.4.0",
"severity": [
{
"score": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N",
"type": "CVSS_V3"
}
],
"summary": "Attribute Injection leading to XSS(Cross-Site-Scripting)"
}
Loading…
Loading…
Experimental. This forecast is provided for visualization only and may change without notice. Do not use it for operational decisions.
Forecast uses a logistic model when the trend is rising, or an exponential decay model when the trend is falling. Fitted via linearized least squares.
Sightings
| Author | Source | Type | Date | Other |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.
Loading…
Loading…