GHSA-6P68-36M6-392R
Vulnerability from github – Published: 2024-03-25 19:45 – Updated: 2024-03-25 22:28
VLAI
Summary
phpMyFAQ Stored Cross-site Scripting at FAQ News Content
Details
Summary
By manipulating the news parameter in a POST request, an attacker can inject malicious JavaScript code. Upon browsing to the compromised news page, the XSS payload triggers.
PoC
- Edit a FAQ news, intercept the request and modify the
newsparameter in the POST body with the following payload:%3cscript%3ealert('xssContent')%3c%2fscript%3e - Browse to the particular news page and the XSS should pop up.
Impact
This allows an attacker to execute arbitrary client side JavaScript within the context of another user's phpMyFAQ session
Severity
4.3 (Medium)
{
"affected": [
{
"package": {
"ecosystem": "Packagist",
"name": "phpmyfaq/phpmyfaq"
},
"ranges": [
{
"events": [
{
"introduced": "3.2.5"
},
{
"fixed": "3.2.6"
}
],
"type": "ECOSYSTEM"
}
],
"versions": [
"3.2.5"
]
}
],
"aliases": [
"CVE-2024-28106"
],
"database_specific": {
"cwe_ids": [
"CWE-79"
],
"github_reviewed": true,
"github_reviewed_at": "2024-03-25T19:45:52Z",
"nvd_published_at": "2024-03-25T19:15:58Z",
"severity": "MODERATE"
},
"details": "### Summary\nBy manipulating the news parameter in a POST request, an attacker can inject malicious JavaScript code. Upon browsing to the compromised news page, the XSS payload triggers.\n\n### PoC\n1. Edit a FAQ news, intercept the request and modify the `news` parameter in the POST body with the following payload: `%3cscript%3ealert(\u0027xssContent\u0027)%3c%2fscript%3e`\n2. Browse to the particular news page and the XSS should pop up.\n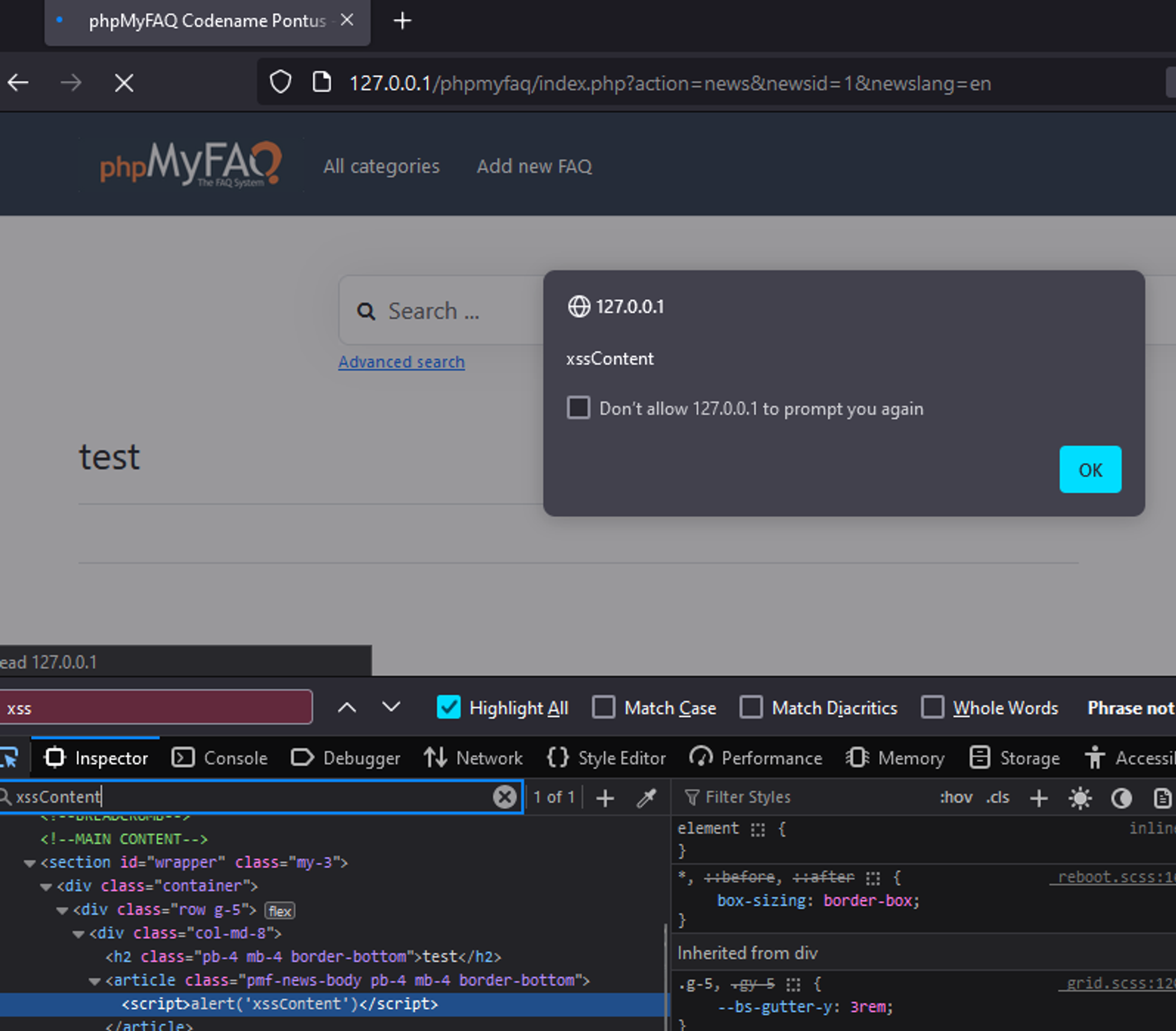\n\n### Impact\nThis allows an attacker to execute arbitrary client side JavaScript within the context of another user\u0027s phpMyFAQ session",
"id": "GHSA-6p68-36m6-392r",
"modified": "2024-03-25T22:28:12Z",
"published": "2024-03-25T19:45:52Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/thorsten/phpMyFAQ/security/advisories/GHSA-6p68-36m6-392r"
},
{
"type": "ADVISORY",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2024-28106"
},
{
"type": "WEB",
"url": "https://github.com/thorsten/phpMyFAQ/commit/c94b3deadd87789389e1fad162bc3dd595c0e15a"
},
{
"type": "PACKAGE",
"url": "https://github.com/thorsten/phpMyFAQ"
}
],
"schema_version": "1.4.0",
"severity": [
{
"score": "CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:U/C:L/I:L/A:L",
"type": "CVSS_V3"
}
],
"summary": "phpMyFAQ Stored Cross-site Scripting at FAQ News Content"
}
Loading…
Loading…
Experimental. This forecast is provided for visualization only and may change without notice. Do not use it for operational decisions.
Forecast uses a logistic model when the trend is rising, or an exponential decay model when the trend is falling. Fitted via linearized least squares.
Sightings
| Author | Source | Type | Date | Other |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.
Loading…
Loading…