GHSA-94VP-RMQV-5875
Vulnerability from github – Published: 2020-11-23 19:48 – Updated: 2021-11-19 13:42Impact
An authenticated backend user with the cms.manage_pages, cms.manage_layouts, or cms.manage_partials permissions who would normally not be permitted to provide PHP code to be executed by the CMS due to cms.enableSafeMode being enabled is able to write specific Twig code to escape the Twig sandbox and execute arbitrary PHP.
This is not a problem for anyone that trusts their users with those permissions to normally write & manage PHP within the CMS by not having cms.enableSafeMode enabled, but would be a problem for anyone relying on cms.enableSafeMode to ensure that users with those permissions in production do not have access to write & execute arbitrary PHP.
Patches
Issue has been patched in Build 469 (v1.0.469) and v1.1.0.
Workarounds
Apply https://github.com/octobercms/october/compare/106daa2930de4cebb18732732d47d4056f01dd5b...7cb148c1677373ac30ccfd3069d18098e403e1ca to your installation manually if unable to upgrade to Build 469.
References
Reported by ka1n4t
For more information
If you have any questions or comments about this advisory: * Email us at hello@octobercms.com
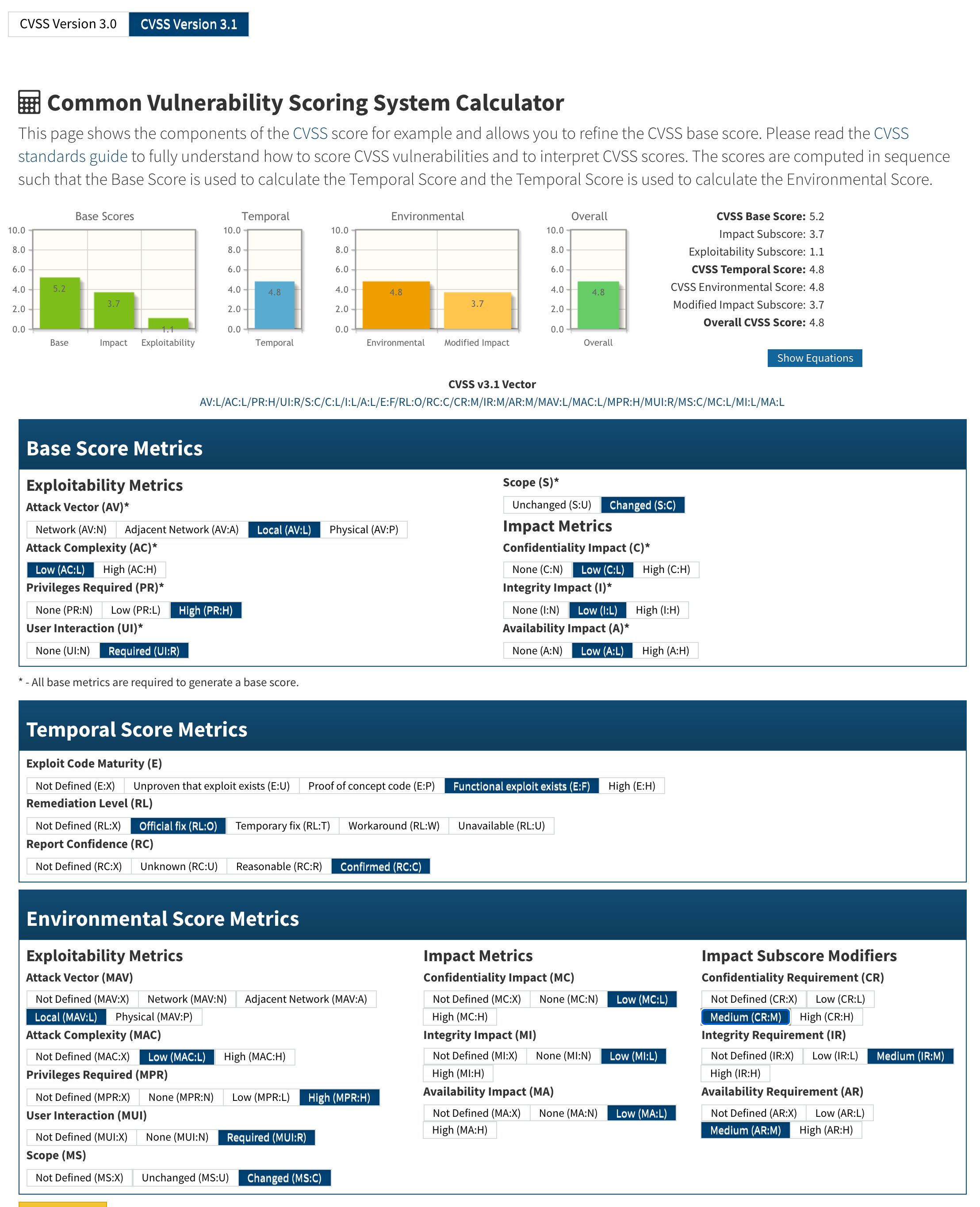
Threat assessment:
{
"affected": [
{
"package": {
"ecosystem": "Packagist",
"name": "october/cms"
},
"ranges": [
{
"events": [
{
"introduced": "1.0.319"
},
{
"fixed": "1.0.469"
}
],
"type": "ECOSYSTEM"
}
]
}
],
"aliases": [
"CVE-2020-15247"
],
"database_specific": {
"cwe_ids": [
"CWE-862"
],
"github_reviewed": true,
"github_reviewed_at": "2020-11-23T19:33:21Z",
"nvd_published_at": "2020-11-23T20:15:00Z",
"severity": "MODERATE"
},
"details": "### Impact\nAn authenticated backend user with the `cms.manage_pages`, `cms.manage_layouts`, or `cms.manage_partials` permissions who would **normally** not be permitted to provide PHP code to be executed by the CMS due to `cms.enableSafeMode` being enabled is able to write specific Twig code to escape the Twig sandbox and execute arbitrary PHP.\n\nThis is not a problem for anyone that trusts their users with those permissions to normally write \u0026 manage PHP within the CMS by not having `cms.enableSafeMode` enabled, but would be a problem for anyone relying on `cms.enableSafeMode` to ensure that users with those permissions in production do not have access to write \u0026 execute arbitrary PHP.\n\n### Patches\nIssue has been patched in Build 469 (v1.0.469) and v1.1.0.\n\n### Workarounds\nApply https://github.com/octobercms/october/compare/106daa2930de4cebb18732732d47d4056f01dd5b...7cb148c1677373ac30ccfd3069d18098e403e1ca to your installation manually if unable to upgrade to Build 469.\n\n### References\nReported by [ka1n4t](https://github.com/ka1n4t)\n\n### For more information\nIf you have any questions or comments about this advisory:\n* Email us at [hello@octobercms.com](mailto:hello@octobercms.com)\n\n### Threat assessment:\n\u003cimg width=\"1108\" alt=\"Screen Shot 2020-10-10 at 1 21 13 PM\" src=\"https://user-images.githubusercontent.com/7253840/95663316-7de28b80-0afb-11eb-999d-a6526cf78709.png\"\u003e",
"id": "GHSA-94vp-rmqv-5875",
"modified": "2021-11-19T13:42:37Z",
"published": "2020-11-23T19:48:27Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/octobercms/october/security/advisories/GHSA-94vp-rmqv-5875"
},
{
"type": "ADVISORY",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2020-15247"
},
{
"type": "WEB",
"url": "https://github.com/octobercms/october/commit/4c650bb775ab849e48202a4923bac93bd74f9982"
},
{
"type": "PACKAGE",
"url": "https://github.com/octobercms/october"
}
],
"schema_version": "1.4.0",
"severity": [
{
"score": "CVSS:3.1/AV:L/AC:L/PR:H/UI:R/S:C/C:L/I:L/A:L",
"type": "CVSS_V3"
}
],
"summary": "Twig Sandbox Escape by authenticated users with access to editing CMS templates when safemode is enabled."
}
Sightings
| Author | Source | Type | Date | Other |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.