GHSA-XHFX-HGMF-V6VP
Vulnerability from github – Published: 2021-03-10 21:07 – Updated: 2025-05-29 23:26Impact
When running on servers that are configured to accept a wildcard as a hostname (i.e. the server routes any request, regardless of the HOST header to an October CMS instance) the potential exists for Host Header Poisoning attacks to succeed. See the following resources for more information on Host Header Poisoning: - https://portswigger.net/web-security/host-header - https://dzone.com/articles/what-is-a-host-header-attack
Patches
A feature has been added in v1.1.2 to allow a set of trusted hosts to be specified in the application.
Workarounds
-
Apply https://github.com/octobercms/library/commit/f86fcbcd066d6f8b939e8fe897409d152b11c3c6 & https://github.com/octobercms/october/commit/f638d3f78cfe91d7f6658820f9d5e424306a3db0 to your installation manually if unable to upgrade to v1.1.2.
-
Check that the configuration setting
cms.linkPolicyis set toforce.
Alternative Workaround
Check to make sure that your web server does not accept any hostname when serving your web application.
- Add an entry called
testing.tldto your computer's host file and direct it to your server's IP address - Open the address
testing.tldin your web browser - Make sure an October CMS website is not available at this address
If an October CMS website is returned, configure your webserver to only allow known hostnames. If you require assistance with this, please contact your server administrator.
References
Reported by Abdullah Hussam
For More Information
If you have any questions or comments about this advisory: * Email us at hello@octobercms.com
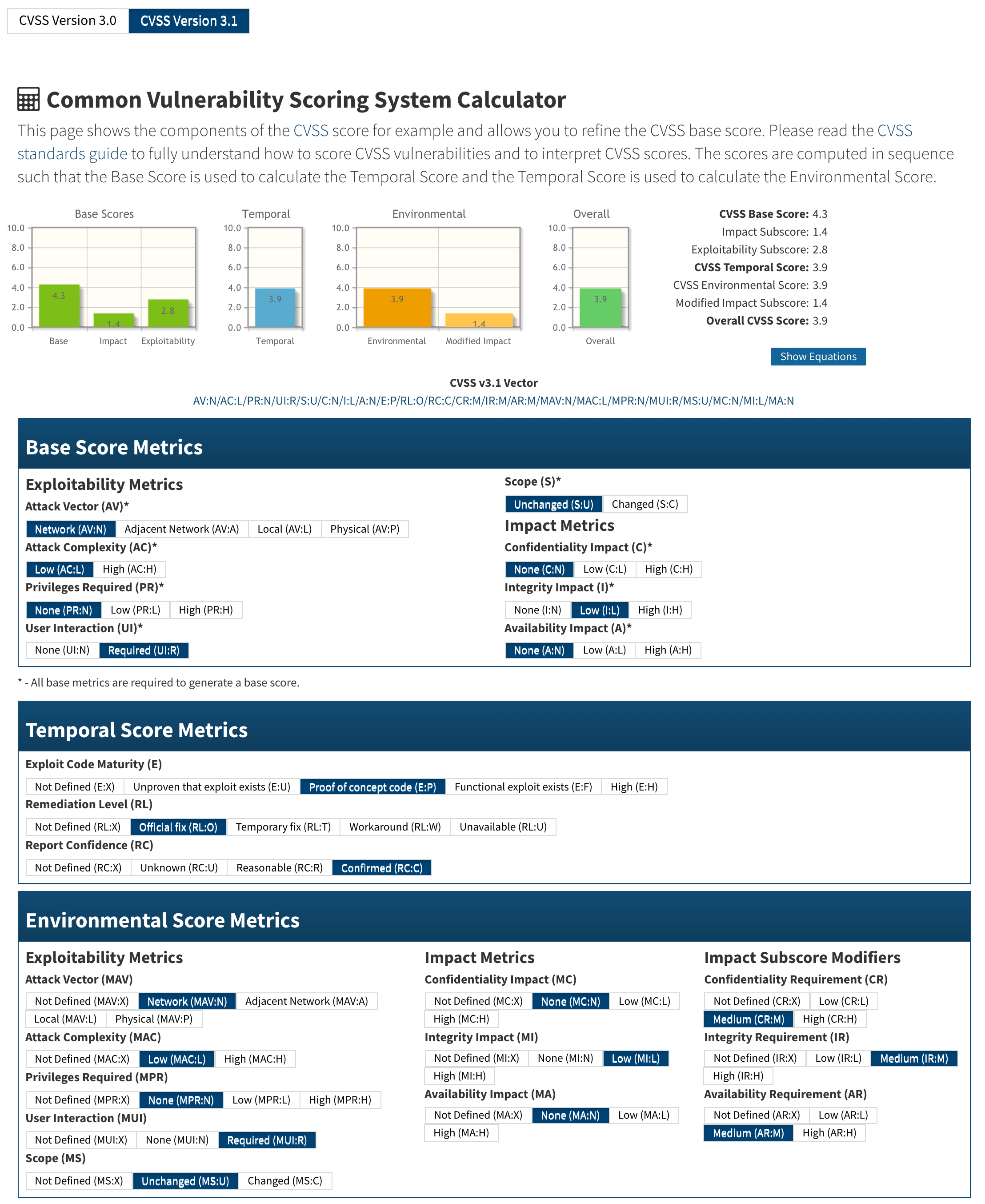
Threat Assessment
{
"affected": [
{
"package": {
"ecosystem": "Packagist",
"name": "october/backend"
},
"ranges": [
{
"events": [
{
"introduced": "0"
},
{
"fixed": "1.1.2"
}
],
"type": "ECOSYSTEM"
}
]
}
],
"aliases": [
"CVE-2021-21265"
],
"database_specific": {
"cwe_ids": [
"CWE-644"
],
"github_reviewed": true,
"github_reviewed_at": "2021-03-10T21:07:08Z",
"nvd_published_at": "2021-03-10T22:15:00Z",
"severity": "LOW"
},
"details": "### Impact\nWhen running on servers that are configured to accept a wildcard as a hostname (i.e. the server routes any request, regardless of the HOST header to an October CMS instance) the potential exists for Host Header Poisoning attacks to succeed. See the following resources for more information on Host Header Poisoning:\n- https://portswigger.net/web-security/host-header\n- https://dzone.com/articles/what-is-a-host-header-attack\n\n### Patches\n\nA feature has been added in v1.1.2 to allow a set of trusted hosts to be specified in the application.\n\n### Workarounds\n\n- Apply https://github.com/octobercms/library/commit/f86fcbcd066d6f8b939e8fe897409d152b11c3c6 \u0026 https://github.com/octobercms/october/commit/f638d3f78cfe91d7f6658820f9d5e424306a3db0 to your installation manually if unable to upgrade to v1.1.2.\n\n- Check that the configuration setting `cms.linkPolicy` is set to `force`.\n\n### Alternative Workaround\n\nCheck to make sure that your web server does not accept any hostname when serving your web application.\n\n1. Add an entry called `testing.tld` to your computer\u0027s host file and direct it to your server\u0027s IP address\n2. Open the address `testing.tld` in your web browser\n3. Make sure an October CMS website is not available at this address\n\nIf an October CMS website is returned, configure your webserver to only allow known hostnames. If you require assistance with this, please contact your server administrator.\n\n### References\n\nReported by [Abdullah Hussam](https://github.com/ahussam)\n\n### For More Information\n\nIf you have any questions or comments about this advisory:\n* Email us at [hello@octobercms.com](mailto:hello@octobercms.com)\n\n### Threat Assessment\n\u003cimg width=\"1108\" alt=\"Screen Shot 2021-01-15 at 4 12 57 PM\" src=\"https://user-images.githubusercontent.com/7253840/104783859-92fb3600-574c-11eb-9e21-c0dc05d230a9.png\"\u003e",
"id": "GHSA-xhfx-hgmf-v6vp",
"modified": "2025-05-29T23:26:01Z",
"published": "2021-03-10T21:07:25Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/octobercms/october/security/advisories/GHSA-xhfx-hgmf-v6vp"
},
{
"type": "ADVISORY",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2021-21265"
},
{
"type": "WEB",
"url": "https://github.com/octobercms/library/commit/f29865ae3db7a03be7c49294cd93980ec457f10d"
},
{
"type": "WEB",
"url": "https://github.com/octobercms/library/commit/f86fcbcd066d6f8b939e8fe897409d152b11c3c6"
},
{
"type": "WEB",
"url": "https://github.com/octobercms/october/commit/555ab61f2313f45d7d5d138656420ead536c5d30"
},
{
"type": "WEB",
"url": "https://github.com/octobercms/october/commit/f638d3f78cfe91d7f6658820f9d5e424306a3db0"
},
{
"type": "WEB",
"url": "https://packagist.org/packages/october/backend"
}
],
"schema_version": "1.4.0",
"severity": [],
"summary": "October CMS vulnerable to Potential Host Header Poisoning on misconfigured servers"
}
Sightings
| Author | Source | Type | Date |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.