CVE-2024-52291 (GCVE-0-2024-52291)
Vulnerability from cvelistv5 – Published: 2024-11-13 16:12 – Updated: 2024-11-13 18:52
VLAI
Title
Craft has a Local File System Validation Bypass Leading to File Overwrite, Sensitive File Access, and Potential Code Execution
Summary
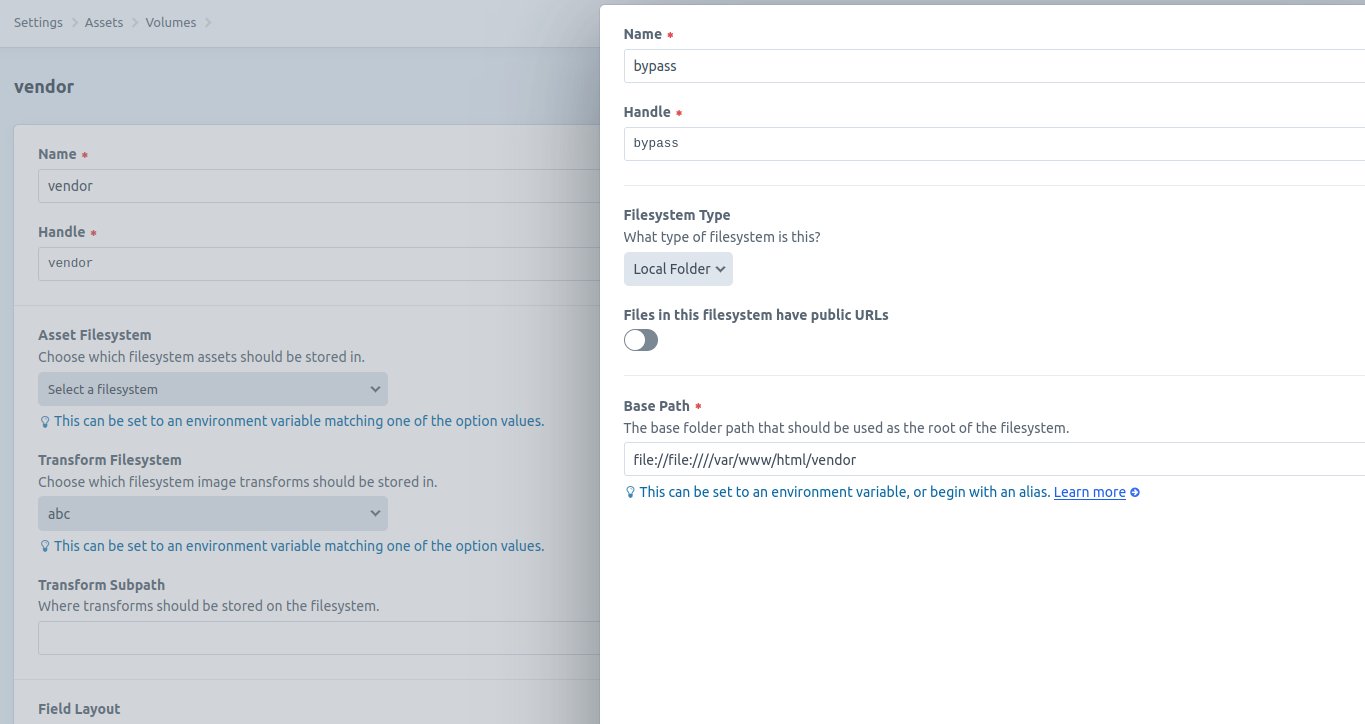
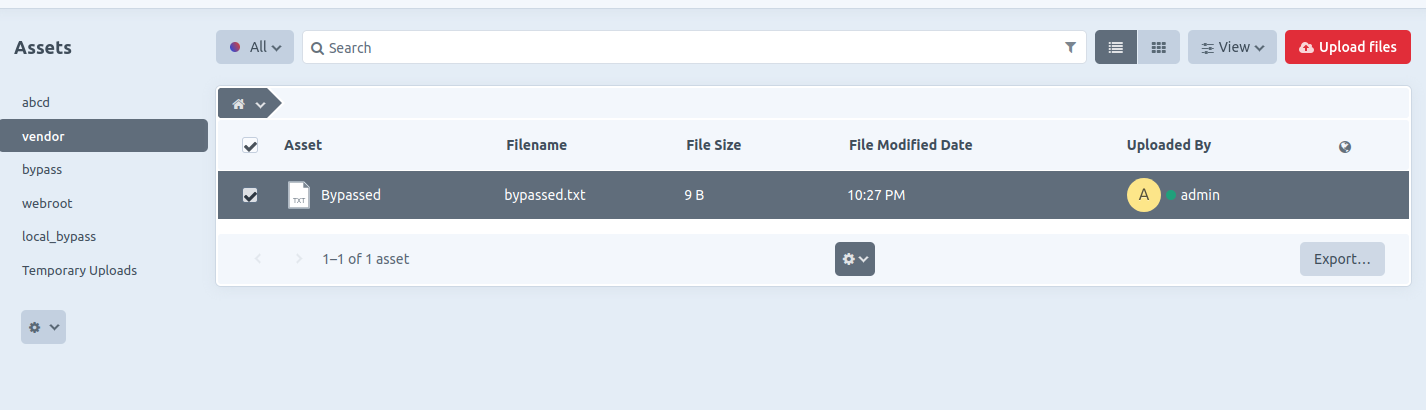
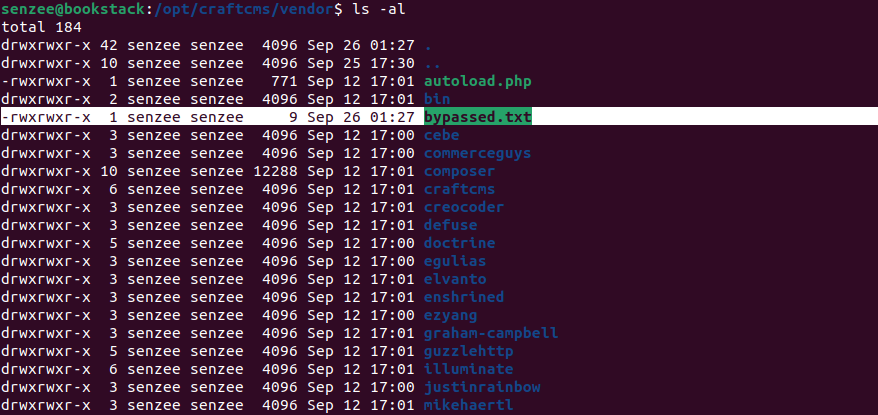
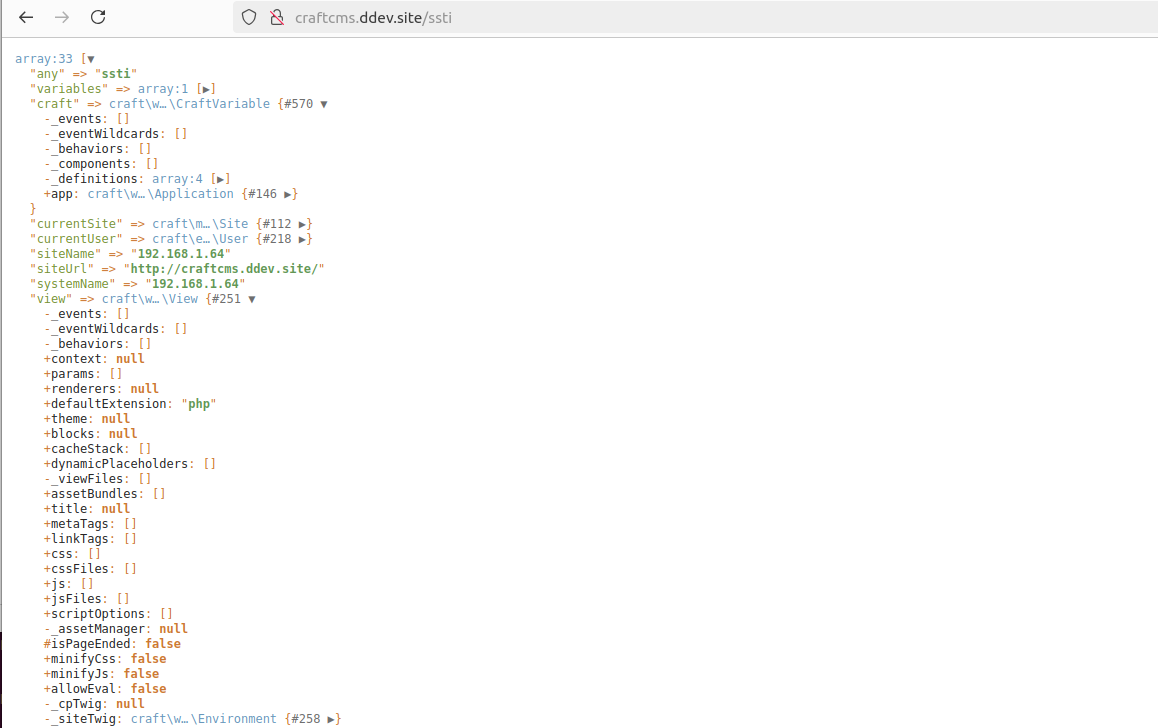
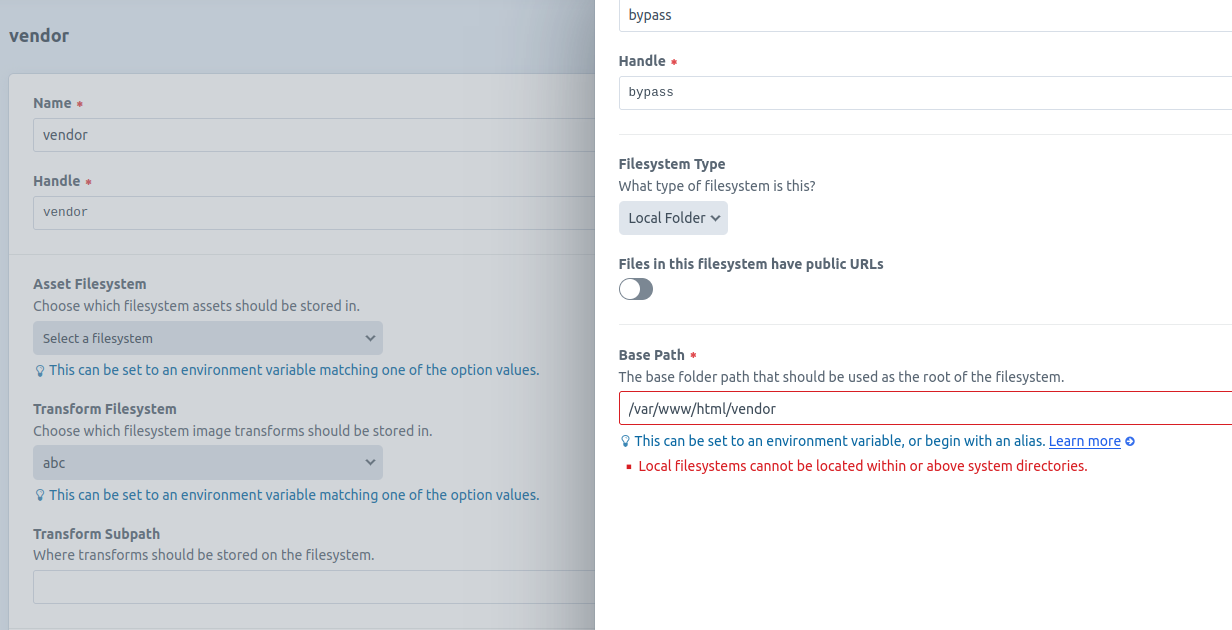
Craft is a content management system (CMS). A vulnerability in CraftCMS allows an attacker to bypass local file system validation by utilizing a double file:// scheme (e.g., file://file:////). This enables the attacker to specify sensitive folders as the file system, leading to potential file overwriting through malicious uploads, unauthorized access to sensitive files, and, under certain conditions, remote code execution (RCE) via Server-Side Template Injection (SSTI) payloads. Note that this will only work if you have an authenticated administrator account with allowAdminChanges enabled. This is fixed in 5.4.6 and 4.12.5.
Severity
8.5 (High)
CWE
- CWE-22 - Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal')
Assigner
References
1 reference
| URL | Tags |
|---|---|
| https://github.com/craftcms/cms/security/advisori… | x_refsource_CONFIRM |
Impacted products
{
"containers": {
"adp": [
{
"affected": [
{
"cpes": [
"cpe:2.3:a:craftcms:craft_cms:*:*:*:*:*:*:*:*"
],
"defaultStatus": "unknown",
"product": "craft_cms",
"vendor": "craftcms",
"versions": [
{
"lessThanOrEqual": "5.0.0-RC1",
"status": "affected",
"version": "0",
"versionType": "custom"
},
{
"lessThan": "5.4.6",
"status": "affected",
"version": "0",
"versionType": "custom"
},
{
"lessThanOrEqual": "4.0.0-RC1",
"status": "affected",
"version": "0",
"versionType": "custom"
},
{
"lessThan": "4.12.5",
"status": "affected",
"version": "0",
"versionType": "custom"
}
]
}
],
"metrics": [
{
"other": {
"content": {
"id": "CVE-2024-52291",
"options": [
{
"Exploitation": "poc"
},
{
"Automatable": "no"
},
{
"Technical Impact": "total"
}
],
"role": "CISA Coordinator",
"timestamp": "2024-11-13T18:50:50.793331Z",
"version": "2.0.3"
},
"type": "ssvc"
}
}
],
"providerMetadata": {
"dateUpdated": "2024-11-13T18:52:15.774Z",
"orgId": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"shortName": "CISA-ADP"
},
"title": "CISA ADP Vulnrichment"
}
],
"cna": {
"affected": [
{
"product": "cms",
"vendor": "craftcms",
"versions": [
{
"status": "affected",
"version": "\u003e= 5.0.0-RC1, \u003c 5.4.6"
},
{
"status": "affected",
"version": "\u003e= 4.0.0-RC1, \u003c 4.12.5"
}
]
}
],
"descriptions": [
{
"lang": "en",
"value": "Craft is a content management system (CMS). A vulnerability in CraftCMS allows an attacker to bypass local file system validation by utilizing a double file:// scheme (e.g., file://file:////). This enables the attacker to specify sensitive folders as the file system, leading to potential file overwriting through malicious uploads, unauthorized access to sensitive files, and, under certain conditions, remote code execution (RCE) via Server-Side Template Injection (SSTI) payloads. Note that this will only work if you have an authenticated administrator account with allowAdminChanges enabled. This is fixed in 5.4.6 and 4.12.5."
}
],
"metrics": [
{
"cvssV3_1": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:C/C:H/I:H/A:H",
"version": "3.1"
}
}
],
"problemTypes": [
{
"descriptions": [
{
"cweId": "CWE-22",
"description": "CWE-22: Improper Limitation of a Pathname to a Restricted Directory (\u0027Path Traversal\u0027)",
"lang": "en",
"type": "CWE"
}
]
}
],
"providerMetadata": {
"dateUpdated": "2024-11-13T16:12:14.803Z",
"orgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"shortName": "GitHub_M"
},
"references": [
{
"name": "https://github.com/craftcms/cms/security/advisories/GHSA-jrh5-vhr9-qh7q",
"tags": [
"x_refsource_CONFIRM"
],
"url": "https://github.com/craftcms/cms/security/advisories/GHSA-jrh5-vhr9-qh7q"
}
],
"source": {
"advisory": "GHSA-jrh5-vhr9-qh7q",
"discovery": "UNKNOWN"
},
"title": "Craft has a Local File System Validation Bypass Leading to File Overwrite, Sensitive File Access, and Potential Code Execution"
}
},
"cveMetadata": {
"assignerOrgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"assignerShortName": "GitHub_M",
"cveId": "CVE-2024-52291",
"datePublished": "2024-11-13T16:12:14.803Z",
"dateReserved": "2024-11-06T19:00:26.394Z",
"dateUpdated": "2024-11-13T18:52:15.774Z",
"state": "PUBLISHED"
},
"dataType": "CVE_RECORD",
"dataVersion": "5.1",
"vulnerability-lookup:meta": {
"epss": {
"cve": "CVE-2024-52291",
"date": "2026-05-30",
"epss": "0.00128",
"percentile": "0.31765"
},
"fkie_nvd": {
"configurations": "[{\"nodes\": [{\"operator\": \"OR\", \"negate\": false, \"cpeMatch\": [{\"vulnerable\": true, \"criteria\": \"cpe:2.3:a:craftcms:craft_cms:*:*:*:*:*:*:*:*\", \"versionStartExcluding\": \"4.0.0\", \"versionEndExcluding\": \"4.12.5\", \"matchCriteriaId\": \"D75081F6-DA85-4F2D-B57B-5F4E8864B8F8\"}, {\"vulnerable\": true, \"criteria\": \"cpe:2.3:a:craftcms:craft_cms:*:*:*:*:*:*:*:*\", \"versionStartExcluding\": \"5.0.0\", \"versionEndExcluding\": \"5.4.6\", \"matchCriteriaId\": \"E8C229F2-C3B1-4715-97FD-53AD88FB124F\"}, {\"vulnerable\": true, \"criteria\": \"cpe:2.3:a:craftcms:craft_cms:4.0.0:rc1:*:*:*:*:*:*\", \"matchCriteriaId\": \"CC2F40FC-7C27-456A-B16D-679410D1D5CF\"}, {\"vulnerable\": true, \"criteria\": \"cpe:2.3:a:craftcms:craft_cms:4.0.0:rc2:*:*:*:*:*:*\", \"matchCriteriaId\": \"FBAA8227-04F8-404C-907B-B0162B325F5A\"}, {\"vulnerable\": true, \"criteria\": \"cpe:2.3:a:craftcms:craft_cms:4.0.0:rc3:*:*:*:*:*:*\", \"matchCriteriaId\": \"21B28E2C-327A-4CE6-ACAD-97E459712A55\"}, {\"vulnerable\": true, \"criteria\": \"cpe:2.3:a:craftcms:craft_cms:5.0.0:rc1:*:*:*:*:*:*\", \"matchCriteriaId\": \"8D8E02D1-601A-4E2B-B619-4775BFDB72D0\"}]}]}]",
"descriptions": "[{\"lang\": \"en\", \"value\": \"Craft is a content management system (CMS). A vulnerability in CraftCMS allows an attacker to bypass local file system validation by utilizing a double file:// scheme (e.g., file://file:////). This enables the attacker to specify sensitive folders as the file system, leading to potential file overwriting through malicious uploads, unauthorized access to sensitive files, and, under certain conditions, remote code execution (RCE) via Server-Side Template Injection (SSTI) payloads. Note that this will only work if you have an authenticated administrator account with allowAdminChanges enabled. This is fixed in 5.4.6 and 4.12.5.\"}, {\"lang\": \"es\", \"value\": \"Craft es un sistema de gesti\\u00f3n de contenido (CMS). Una vulnerabilidad en CraftCMS permite a un atacante eludir la validaci\\u00f3n del sistema de archivos local mediante un esquema file:// doble (por ejemplo, file://file:////). Esto permite al atacante especificar carpetas confidenciales como sistema de archivos, lo que lleva a una posible sobrescritura de archivos mediante cargas maliciosas, acceso no autorizado a archivos confidenciales y, en determinadas condiciones, ejecuci\\u00f3n remota de c\\u00f3digo (RCE) mediante payloads de Server-Side Template Injection (SSTI). Tenga en cuenta que esto solo funcionar\\u00e1 si tiene una cuenta de administrador autenticada con allowAdminChanges habilitado. Esto se solucion\\u00f3 en 5.4.6 y 4.12.5.\"}]",
"id": "CVE-2024-52291",
"lastModified": "2024-11-19T18:06:42.973",
"metrics": "{\"cvssMetricV31\": [{\"source\": \"security-advisories@github.com\", \"type\": \"Secondary\", \"cvssData\": {\"version\": \"3.1\", \"vectorString\": \"CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:C/C:H/I:H/A:H\", \"baseScore\": 8.4, \"baseSeverity\": \"HIGH\", \"attackVector\": \"NETWORK\", \"attackComplexity\": \"LOW\", \"privilegesRequired\": \"HIGH\", \"userInteraction\": \"REQUIRED\", \"scope\": \"CHANGED\", \"confidentialityImpact\": \"HIGH\", \"integrityImpact\": \"HIGH\", \"availabilityImpact\": \"HIGH\"}, \"exploitabilityScore\": 1.7, \"impactScore\": 6.0}, {\"source\": \"nvd@nist.gov\", \"type\": \"Primary\", \"cvssData\": {\"version\": \"3.1\", \"vectorString\": \"CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H\", \"baseScore\": 7.2, \"baseSeverity\": \"HIGH\", \"attackVector\": \"NETWORK\", \"attackComplexity\": \"LOW\", \"privilegesRequired\": \"HIGH\", \"userInteraction\": \"NONE\", \"scope\": \"UNCHANGED\", \"confidentialityImpact\": \"HIGH\", \"integrityImpact\": \"HIGH\", \"availabilityImpact\": \"HIGH\"}, \"exploitabilityScore\": 1.2, \"impactScore\": 5.9}]}",
"published": "2024-11-13T17:15:12.087",
"references": "[{\"url\": \"https://github.com/craftcms/cms/security/advisories/GHSA-jrh5-vhr9-qh7q\", \"source\": \"security-advisories@github.com\", \"tags\": [\"Exploit\", \"Vendor Advisory\"]}]",
"sourceIdentifier": "security-advisories@github.com",
"vulnStatus": "Analyzed",
"weaknesses": "[{\"source\": \"security-advisories@github.com\", \"type\": \"Primary\", \"description\": [{\"lang\": \"en\", \"value\": \"CWE-22\"}]}]"
},
"nvd": "{\"cve\":{\"id\":\"CVE-2024-52291\",\"sourceIdentifier\":\"security-advisories@github.com\",\"published\":\"2024-11-13T17:15:12.087\",\"lastModified\":\"2024-11-19T18:06:42.973\",\"vulnStatus\":\"Analyzed\",\"cveTags\":[],\"descriptions\":[{\"lang\":\"en\",\"value\":\"Craft is a content management system (CMS). A vulnerability in CraftCMS allows an attacker to bypass local file system validation by utilizing a double file:// scheme (e.g., file://file:////). This enables the attacker to specify sensitive folders as the file system, leading to potential file overwriting through malicious uploads, unauthorized access to sensitive files, and, under certain conditions, remote code execution (RCE) via Server-Side Template Injection (SSTI) payloads. Note that this will only work if you have an authenticated administrator account with allowAdminChanges enabled. This is fixed in 5.4.6 and 4.12.5.\"},{\"lang\":\"es\",\"value\":\"Craft es un sistema de gesti\u00f3n de contenido (CMS). Una vulnerabilidad en CraftCMS permite a un atacante eludir la validaci\u00f3n del sistema de archivos local mediante un esquema file:// doble (por ejemplo, file://file:////). Esto permite al atacante especificar carpetas confidenciales como sistema de archivos, lo que lleva a una posible sobrescritura de archivos mediante cargas maliciosas, acceso no autorizado a archivos confidenciales y, en determinadas condiciones, ejecuci\u00f3n remota de c\u00f3digo (RCE) mediante payloads de Server-Side Template Injection (SSTI). Tenga en cuenta que esto solo funcionar\u00e1 si tiene una cuenta de administrador autenticada con allowAdminChanges habilitado. Esto se solucion\u00f3 en 5.4.6 y 4.12.5.\"}],\"metrics\":{\"cvssMetricV31\":[{\"source\":\"security-advisories@github.com\",\"type\":\"Secondary\",\"cvssData\":{\"version\":\"3.1\",\"vectorString\":\"CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:C/C:H/I:H/A:H\",\"baseScore\":8.4,\"baseSeverity\":\"HIGH\",\"attackVector\":\"NETWORK\",\"attackComplexity\":\"LOW\",\"privilegesRequired\":\"HIGH\",\"userInteraction\":\"REQUIRED\",\"scope\":\"CHANGED\",\"confidentialityImpact\":\"HIGH\",\"integrityImpact\":\"HIGH\",\"availabilityImpact\":\"HIGH\"},\"exploitabilityScore\":1.7,\"impactScore\":6.0},{\"source\":\"nvd@nist.gov\",\"type\":\"Primary\",\"cvssData\":{\"version\":\"3.1\",\"vectorString\":\"CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H\",\"baseScore\":7.2,\"baseSeverity\":\"HIGH\",\"attackVector\":\"NETWORK\",\"attackComplexity\":\"LOW\",\"privilegesRequired\":\"HIGH\",\"userInteraction\":\"NONE\",\"scope\":\"UNCHANGED\",\"confidentialityImpact\":\"HIGH\",\"integrityImpact\":\"HIGH\",\"availabilityImpact\":\"HIGH\"},\"exploitabilityScore\":1.2,\"impactScore\":5.9}]},\"weaknesses\":[{\"source\":\"security-advisories@github.com\",\"type\":\"Primary\",\"description\":[{\"lang\":\"en\",\"value\":\"CWE-22\"}]}],\"configurations\":[{\"nodes\":[{\"operator\":\"OR\",\"negate\":false,\"cpeMatch\":[{\"vulnerable\":true,\"criteria\":\"cpe:2.3:a:craftcms:craft_cms:*:*:*:*:*:*:*:*\",\"versionStartExcluding\":\"4.0.0\",\"versionEndExcluding\":\"4.12.5\",\"matchCriteriaId\":\"D75081F6-DA85-4F2D-B57B-5F4E8864B8F8\"},{\"vulnerable\":true,\"criteria\":\"cpe:2.3:a:craftcms:craft_cms:*:*:*:*:*:*:*:*\",\"versionStartExcluding\":\"5.0.0\",\"versionEndExcluding\":\"5.4.6\",\"matchCriteriaId\":\"E8C229F2-C3B1-4715-97FD-53AD88FB124F\"},{\"vulnerable\":true,\"criteria\":\"cpe:2.3:a:craftcms:craft_cms:4.0.0:rc1:*:*:*:*:*:*\",\"matchCriteriaId\":\"CC2F40FC-7C27-456A-B16D-679410D1D5CF\"},{\"vulnerable\":true,\"criteria\":\"cpe:2.3:a:craftcms:craft_cms:4.0.0:rc2:*:*:*:*:*:*\",\"matchCriteriaId\":\"FBAA8227-04F8-404C-907B-B0162B325F5A\"},{\"vulnerable\":true,\"criteria\":\"cpe:2.3:a:craftcms:craft_cms:4.0.0:rc3:*:*:*:*:*:*\",\"matchCriteriaId\":\"21B28E2C-327A-4CE6-ACAD-97E459712A55\"},{\"vulnerable\":true,\"criteria\":\"cpe:2.3:a:craftcms:craft_cms:5.0.0:rc1:*:*:*:*:*:*\",\"matchCriteriaId\":\"8D8E02D1-601A-4E2B-B619-4775BFDB72D0\"}]}]}],\"references\":[{\"url\":\"https://github.com/craftcms/cms/security/advisories/GHSA-jrh5-vhr9-qh7q\",\"source\":\"security-advisories@github.com\",\"tags\":[\"Exploit\",\"Vendor Advisory\"]}]}}",
"vulnrichment": {
"containers": "{\"adp\": [{\"title\": \"CISA ADP Vulnrichment\", \"metrics\": [{\"other\": {\"type\": \"ssvc\", \"content\": {\"id\": \"CVE-2024-52291\", \"role\": \"CISA Coordinator\", \"options\": [{\"Exploitation\": \"poc\"}, {\"Automatable\": \"no\"}, {\"Technical Impact\": \"total\"}], \"version\": \"2.0.3\", \"timestamp\": \"2024-11-13T18:50:50.793331Z\"}}}], \"affected\": [{\"cpes\": [\"cpe:2.3:a:craftcms:craft_cms:*:*:*:*:*:*:*:*\"], \"vendor\": \"craftcms\", \"product\": \"craft_cms\", \"versions\": [{\"status\": \"affected\", \"version\": \"0\", \"versionType\": \"custom\", \"lessThanOrEqual\": \"5.0.0-RC1\"}, {\"status\": \"affected\", \"version\": \"0\", \"lessThan\": \"5.4.6\", \"versionType\": \"custom\"}, {\"status\": \"affected\", \"version\": \"0\", \"versionType\": \"custom\", \"lessThanOrEqual\": \"4.0.0-RC1\"}, {\"status\": \"affected\", \"version\": \"0\", \"lessThan\": \"4.12.5\", \"versionType\": \"custom\"}], \"defaultStatus\": \"unknown\"}], \"providerMetadata\": {\"orgId\": \"134c704f-9b21-4f2e-91b3-4a467353bcc0\", \"shortName\": \"CISA-ADP\", \"dateUpdated\": \"2024-11-13T18:52:03.472Z\"}}], \"cna\": {\"title\": \"Craft has a Local File System Validation Bypass Leading to File Overwrite, Sensitive File Access, and Potential Code Execution\", \"source\": {\"advisory\": \"GHSA-jrh5-vhr9-qh7q\", \"discovery\": \"UNKNOWN\"}, \"metrics\": [{\"cvssV3_1\": {\"scope\": \"CHANGED\", \"version\": \"3.1\", \"baseScore\": 8.5, \"attackVector\": \"NETWORK\", \"baseSeverity\": \"HIGH\", \"vectorString\": \"CVSS:3.1/AV:N/AC:L/PR:H/UI:R/S:C/C:H/I:H/A:H\", \"integrityImpact\": \"HIGH\", \"userInteraction\": \"REQUIRED\", \"attackComplexity\": \"LOW\", \"availabilityImpact\": \"HIGH\", \"privilegesRequired\": \"HIGH\", \"confidentialityImpact\": \"HIGH\"}}], \"affected\": [{\"vendor\": \"craftcms\", \"product\": \"cms\", \"versions\": [{\"status\": \"affected\", \"version\": \"\u003e= 5.0.0-RC1, \u003c 5.4.6\"}, {\"status\": \"affected\", \"version\": \"\u003e= 4.0.0-RC1, \u003c 4.12.5\"}]}], \"references\": [{\"url\": \"https://github.com/craftcms/cms/security/advisories/GHSA-jrh5-vhr9-qh7q\", \"name\": \"https://github.com/craftcms/cms/security/advisories/GHSA-jrh5-vhr9-qh7q\", \"tags\": [\"x_refsource_CONFIRM\"]}], \"descriptions\": [{\"lang\": \"en\", \"value\": \"Craft is a content management system (CMS). A vulnerability in CraftCMS allows an attacker to bypass local file system validation by utilizing a double file:// scheme (e.g., file://file:////). This enables the attacker to specify sensitive folders as the file system, leading to potential file overwriting through malicious uploads, unauthorized access to sensitive files, and, under certain conditions, remote code execution (RCE) via Server-Side Template Injection (SSTI) payloads. Note that this will only work if you have an authenticated administrator account with allowAdminChanges enabled. This is fixed in 5.4.6 and 4.12.5.\"}], \"problemTypes\": [{\"descriptions\": [{\"lang\": \"en\", \"type\": \"CWE\", \"cweId\": \"CWE-22\", \"description\": \"CWE-22: Improper Limitation of a Pathname to a Restricted Directory (\u0027Path Traversal\u0027)\"}]}], \"providerMetadata\": {\"orgId\": \"a0819718-46f1-4df5-94e2-005712e83aaa\", \"shortName\": \"GitHub_M\", \"dateUpdated\": \"2024-11-13T16:12:14.803Z\"}}}",
"cveMetadata": "{\"cveId\": \"CVE-2024-52291\", \"state\": \"PUBLISHED\", \"dateUpdated\": \"2024-11-13T18:52:15.774Z\", \"dateReserved\": \"2024-11-06T19:00:26.394Z\", \"assignerOrgId\": \"a0819718-46f1-4df5-94e2-005712e83aaa\", \"datePublished\": \"2024-11-13T16:12:14.803Z\", \"assignerShortName\": \"GitHub_M\"}",
"dataType": "CVE_RECORD",
"dataVersion": "5.1"
}
}
}
Loading…
Loading…
Experimental. This forecast is provided for visualization only and may change without notice. Do not use it for operational decisions.
Forecast uses a logistic model when the trend is rising, or an exponential decay model when the trend is falling. Fitted via linearized least squares.
Sightings
| Author | Source | Type | Date | Other |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or observed by the user.
- Confirmed: The vulnerability has been validated from an analyst's perspective.
- Published Proof of Concept: A public proof of concept is available for this vulnerability.
- Exploited: The vulnerability was observed as exploited by the user who reported the sighting.
- Patched: The vulnerability was observed as successfully patched by the user who reported the sighting.
- Not exploited: The vulnerability was not observed as exploited by the user who reported the sighting.
- Not confirmed: The user expressed doubt about the validity of the vulnerability.
- Not patched: The vulnerability was not observed as successfully patched by the user who reported the sighting.
Loading…
Loading…
 With the double
With the double